The History of Hacking: From Phone Phreaking to Ransomware (and What It Teaches Us Today)
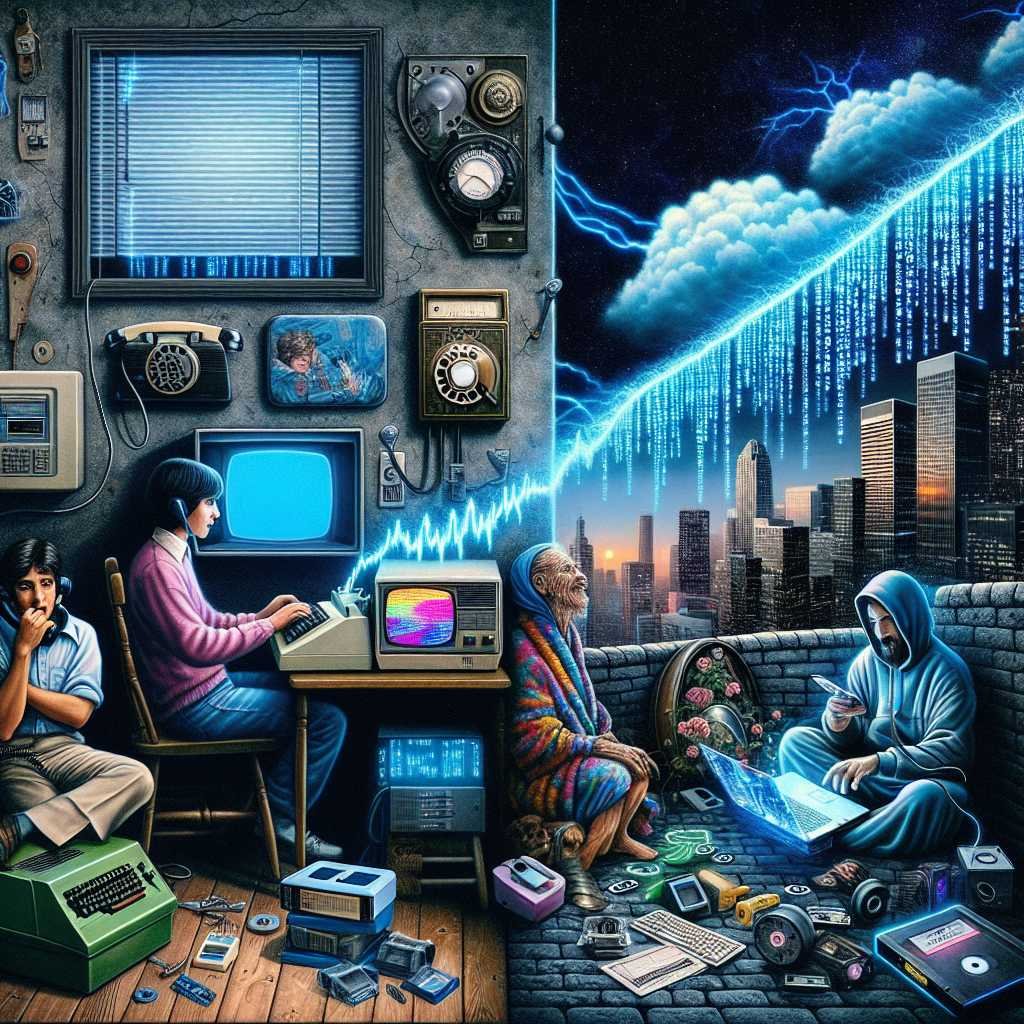
What if I told you hacking started with a toy whistle and a curious ear? Long before memes about “hackers in hoodies,” people with soldering irons and a knack for sound were playing with phone networks. They weren’t stealing millions. They were exploring. Then the internet arrived. Curiosity met connectivity. And hacking shifted—from a subculture of tinkerers to a global cybercrime industry with ransomware gangs and nation-states in the mix.
If you’re wondering how we got from blue boxes to billion‑dollar breaches, you’re in the right place. Let’s tour the pivotal moments, the culture shifts, and the hard lessons that can make you safer right now.
What “Hacking” Really Means (and Why Words Matter)
We use “hacking” for a lot of things. That muddies the conversation. Here’s a simple breakdown:
- Hacker: Traditionally, a person who loves exploring systems, pushing limits, and learning how things work. Curiosity drives them.
- Ethical hacker (white hat): Tests defenses to improve security, with permission.
- Gray hat: May cross lines without malicious intent (e.g., probing a system and then reporting it).
- Cybercriminal (black hat): Hacks for money, power, or disruption.
The hacker ethic—share knowledge, improve systems, respect users—has shaped security for decades. The line gets blurred when exploration turns into exploitation.
For an early glimpse of this ethic, see the Chaos Computer Club’s “Hacker Ethics” manifesto, a foundational text for modern hacker culture: CCC Hacker Ethics.
The Analog Origins: Phone Phreaking in the 1960s–70s
Before the internet, there were phone networks. They had a problem: the same lines carried both voice and control signals. Phreakers learned that certain tones could “talk” to the network.
- 2600 Hz, a key frequency, became iconic after some phreakers discovered a toy cereal-box whistle could mimic it.
- “Blue boxes” generated tones to trick long-distance routing. This was illegal, but for many, the thrill was about understanding systems, not profit.
- This scene influenced future tech leaders. Steve Wozniak and Steve Jobs tinkered with blue boxes before founding Apple. The curiosity, the DIY spirit, the belief that you can bend systems to your will—that’s the DNA of Silicon Valley.
Want to dive deeper into this era? The Computer History Museum has an excellent overview: Phone Phreaking: A 1960s Hack. Wired also digs into the era’s “blue box” lore: The Blue Box Story.
Why it matters: Early systems trusted users by default. Attackers exploited that trust. That pattern repeats, again and again.
The 1980s: Modems, BBS Culture, and the First Cyber Laws
As modems spread, hacking moved from whistles to phone lines and mainframes.
- Bulletin Board Systems (BBS) let tinkerers meet, trade tips, and—sometimes—learn questionable tricks.
- The “414s,” a group of teenagers from Milwaukee, made headlines in 1983 for breaking into high‑profile systems. The mythos of the hacker was born.
- WarGames (1983) captured the public imagination—and fear—of remote intrusion.
- The Computer Fraud and Abuse Act (CFAA) passed in 1986, defining new computer crimes in the U.S. Details here: DOJ on the CFAA.
- In 1988, the Morris Worm—the first major internet worm—took down about 10% of the then‑small internet. It exposed how fragile shared systems could be. Read more: The Morris Worm (Computer History Museum).
Hacker communities organized too. The Chaos Computer Club (CCC) formed in Germany, championing transparency and public-interest security research. Their impact on hacker ethics still resonates.
The 1990s: The Internet Arrives, and Hacking Goes Mainstream
Dial‑up gave way to the web. Suddenly, everyone had a front door—and attackers started knocking.
- Kevin Mitnick became a media figure as law enforcement chased him across networks. His story spotlighted social engineering, which still powers many breaches.
- AOL became a training ground for phishers. Early kits like “AOHell” made scams accessible to novices, foreshadowing today’s “as‑a‑service” crime economy.
- Security and hacker culture matured. DEF CON launched in 1993; it remains a bellwether of the community: DEF CON History.
- In 1998, the L0pht hacker collective testified to the U.S. Senate that they could take down the internet in 30 minutes. Lawmakers took note. The hearing pushed responsible disclosure into the mainstream: Remembering L0pht’s 1998 Testimony (EFF).
- Malware evolved from hobbyist pranks to costly outbreaks. The 1999 Melissa virus spread via Word macros and email, causing significant damage. FBI case history: Melissa Virus (FBI).
Lesson: Connectivity amplifies both creativity and risk. And humans, not just code, are attack targets.
The 2000s: Worms, Botnets, and the Cybercrime Economy
Always‑on broadband changed the game. So did e‑commerce and online payments.
- ILOVEYOU (2000), Code Red (2001), Nimda (2001), and Slammer (2003) spread at internet speed. They exploited unpatched systems and standard protocols.
- Botnets emerged to power spam, credential theft, and DDoS-for-hire. Crime became scalable.
- Underground markets flourished. Criminals sold stolen cards, exploits, and access to compromised systems. Cybercrime started to look like a business, with roles, SLAs, and—sometimes—customer support.
This era forced defenders to adopt patching discipline, network segmentation, and intrusion detection. It also taught a hard truth: automation favors attackers unless defenders automate too.
The 2010s: Nation‑States and Ransomware Go Big
The 2010s revealed a new dimension: hacking as geopolitical leverage.
- Stuxnet (2010) targeted Iranian nuclear centrifuges. It was a watershed—malware designed to cause physical damage. Background: Stuxnet, the First Digital Weapon (IEEE Spectrum).
- Major breaches became national events: Sony Pictures (2014), the U.S. Office of Personnel Management (2015), and more.
- Russia and Ukraine clashed in cyberspace. NotPetya (2017), disguised as ransomware, wiped data worldwide and disrupted global shipping and logistics. Deep dive: The Untold Story of NotPetya (WIRED).
- WannaCry (2017) exploited a leaked NSA tool (EternalBlue) to spread ransomware across the globe. It crippled hospitals and businesses. Alert recap: CISA on SMBv1 Vulnerabilities.
- Supply chain attacks raised the stakes. SolarWinds (2020) showed how compromising one vendor could open doors into thousands of networks, including government agencies. Advisory: CISA Alert on SolarWinds.
- Consumers felt the shock too. The Equifax breach (2017) exposed data for 147 million people. FTC summary: Equifax Data Breach Settlement.
By the end of the decade, ransomware had matured into a thriving economy. Cryptocurrency enabled fast, cross‑border payments. Ransomware‑as‑a‑Service (RaaS) let affiliates “rent” malware and share profits. Extortion got professional.
The 2020s: Organized Cybercrime at Scale
If the 2010s were the rise of ransomware, the 2020s are its industrialization.
- Colonial Pipeline (2021) put ransomware on the front page. A single breach led to fuel shortages and emergency declarations. The DOJ later seized part of the ransom paid to DarkSide: DOJ Seizes Cryptocurrency from Ransomware Group.
- Modern ransomware uses double and triple extortion. Attackers steal data, encrypt systems, and threaten to leak or DDoS if you don’t pay.
- “Initial Access Brokers” sell footholds into corporate networks. Affiliates then deploy ransomware. It’s specialization at work.
- Leak sites and brand‑name gangs (e.g., LockBit, Conti) turned cybercrime into marketing. Law enforcement takedowns cause disruption, but the ecosystem adapts.
- Remote work, cloud misconfigurations, and sprawling SaaS apps widened the attack surface. Meanwhile, criminals use convincing voice clones and deepfakes to add pressure during extortion—an unsettling human twist.
To track trends, check the EU’s threat landscape report: ENISA Threat Landscape. For losses by category, see the FBI’s IC3 program: FBI IC3 Public Service Announcements.
How Hacker Culture Shaped Security, Ethics, and Activism
It’s easy to focus on crimes and forget the community that built security as a craft.
- Bug bounties normalized. Companies now pay researchers to report flaws. Even the Pentagon ran a program to crowdsource bugs: “Hack the Pentagon”.
- Coordinated vulnerability disclosure and CVEs improved how we fix issues at scale.
- Open-source security tools and shared knowledge strengthened defenders.
- Hacktivism, from the Arab Spring era to various causes, showed hacking as protest—though tactics and legality vary widely.
Here’s why that matters: The best defense comes from people who understand how systems can fail. Ethical hackers turn curiosity into resilience.
From Curiosity to Cybercrime: Why the Shift Happened
What changed between cereal-box whistles and multimillion‑dollar ransomware attacks?
- Incentives: There’s money to be made, and it’s easier to move it across borders.
- Scale: The internet connected everything. Automation amplifies attacks.
- Markets: You can buy exploits, stolen data, and network access. Crime has supply chains too.
- Complexity: Cloud, APIs, IoT, and remote work expanded the attack surface.
- Defense lag: Patching, identity, and asset management are hard at scale. Attackers exploit gaps that are as much organizational as technical.
Let me explain it with a simple analogy. Think of the internet as a giant city that grew overnight. Some buildings have old locks. Some forgot to close windows. Some have great alarms—but nobody checks them. Attackers don’t need to be geniuses. They just need to walk the blocks and jiggle handles.
What History Teaches Us About Today’s Threats
Looking back gives us practical guidance. Here are the durable lessons that matter most.
1) Trust, but verify (or better, don’t trust by default) – Early phone networks trusted the user. It broke. Legacy IT did too. – Adopt zero trust principles: never assume a device or user is safe just because they’re on your network. – Resource: NIST SP 800‑207: Zero Trust Architecture.
2) Patch fast, patch smart – Worms thrived on unpatched systems. That hasn’t changed. – Set patch SLAs based on risk. Automate where you can. Track exceptions.
3) Identity is the new perimeter – Stolen credentials drive breaches and ransomware. – Use phishing‑resistant MFA and passkeys to defeat many account‑takeover attempts. – Learn more: FIDO Alliance: Passkeys.
4) Assume breach, prepare to recover – Backups, segmentation, and tested restore plans blunt ransomware. – Follow the 3‑2‑1 rule for backups and test restoration. Encrypt backups and isolate them from your domain. – Guidance: CISA Ransomware Guide.
5) People remain the prime target – Social engineering worked for Mitnick. It works better with deepfakes. – Train users to spot phish. Validate unusual requests out of band. Reduce the blast radius with least privilege.
6) Map adversary behavior, not just tools – Tools change; tactics don’t. Use ATT&CK to understand likely steps and add controls at each stage. – Framework: MITRE ATT&CK.
7) Make security an engineering problem, not an IT chore – Build secure defaults. Add guardrails in CI/CD. Scan dependencies. Use SBOMs for visibility. – Reward reporting. Run tabletop exercises. Practice incident response like a fire drill.
If you only do three things this quarter, do these: – Turn on phishing‑resistant MFA for admins and remote access. – Patch internet‑facing systems within days, not weeks. – Test your backups and recovery time. Actually restore a critical system from scratch.
A Quick Timeline of Landmark Hacks and Shifts
- 1960s–70s: Phone phreaking explores the analog core of global telephony.
- 1983: The 414s case and WarGames spark public concern and new laws.
- 1988: Morris Worm exposes internet fragility.
- 1990s: DEF CON, L0pht, and Melissa push security into the mainstream.
- 2000–2003: ILOVEYOU, Code Red, Nimda, Slammer reveal the cost of poor patching.
- 2010: Stuxnet shows cyber‑physical stakes.
- 2014–2017: Sony, OPM, WannaCry, NotPetya, Equifax make cyber risk a board topic.
- 2020–2021: SolarWinds and Colonial Pipeline bring supply chain and critical infrastructure into focus.
Each event nudged security from afterthought to architecture. Each one taught us to reduce implicit trust, act fast, and plan for failure.
The Next Chapter: AI, Quantum, and the Human Factor
Attackers are experimenting with AI to scale social engineering, draft cleaner phishing, and sift stolen data. Defenders use AI to detect anomalies, triage alerts, and spot fraud patterns faster. It’s an arms race—but also an opportunity.
Quantum computing sits on the horizon. It could weaken today’s public‑key cryptography. Planning for post‑quantum algorithms will take years, so inventory your crypto dependencies now. Migration will be more of a logistics challenge than a math one.
The constant in every chapter? People. Culture. Process. Most breaches aren’t zero‑day fireworks. They’re phishing emails, reused passwords, misconfigured cloud buckets, and unpatched servers. Solid fundamentals still win.
Frequently Asked Questions
Q: When did hacking start? – The roots go back to phone phreaking in the 1960s–70s, when people explored the phone system using tone generators. Computer hacking took off in the 1980s with modems and BBS culture.
Q: What was phone phreaking—and was it illegal? – Phreaking used tones to interact with old telephone switching systems. It was illegal because it defrauded phone companies and tampered with networks. Today it’s primarily of historical interest; modern networks no longer work that way. Background: Phone Phreaking (Computer History Museum).
Q: What was the first major computer worm? – The 1988 Morris Worm. It unintentionally caused widespread outages and led to the first conviction under the CFAA. Learn more: The Morris Worm.
Q: What’s the difference between a hacker and a cybercriminal? – “Hacker” originally meant a curious builder/breaker of systems. Cybercriminals use hacking techniques to commit crimes. Many hackers are defenders and researchers who improve security through responsible work.
Q: What is ransomware‑as‑a‑service (RaaS)? – A business model where developers rent ransomware tools to affiliates, who carry out attacks and share profits. It lowered the barrier to entry and helped ransomware scale.
Q: How do hackers make money today? – Ransomware, business email compromise, data theft and resale, crypto theft, DDoS extortion, and selling access to compromised networks. The FBI’s IC3 tracks losses: IC3 PSA.
Q: How can organizations reduce ransomware risk? – Use phishing‑resistant MFA, patch external systems fast, segment networks, secure and test backups, monitor for lateral movement, and rehearse incident response. See: CISA Ransomware Guide.
Q: How do nation‑states use hacking? – Espionage, intellectual property theft, influence operations, and in some cases sabotage of critical infrastructure. The SolarWinds case shows the scope of possible supply‑chain compromises: CISA Advisory.
Q: Are bug bounties worth it? – For many organizations, yes—when combined with a clear disclosure policy and strong remediation process. Even government programs have proven value: Hack the Pentagon.
Q: What are the top cybersecurity basics for individuals? – Use a password manager, enable MFA everywhere, keep devices updated, back up important files, and be skeptical of urgent messages or unexpected attachments. Passkeys are a strong, user‑friendly upgrade: FIDO Passkeys.
The Takeaway
From cereal‑box whistles to nation‑state malware, the story of hacking is a story of systems built on trust—and the people who tested that trust. The same patterns keep repeating: weak defaults, slow patching, human shortcuts. The good news? We know what works. Build with zero trust, protect identities, patch fast, and practice recovery. Invest in people who think like hackers but act like guardians.
If this history helped you see today’s threats more clearly, stick around. I publish practical, human‑friendly security insights you can act on. Subscribe for the next deep dive—and stay a step ahead.
Discover more at InnoVirtuoso.com
I would love some feedback on my writing so if you have any, please don’t hesitate to leave a comment around here or in any platforms that is convenient for you.
For more on tech and other topics, explore InnoVirtuoso.com anytime. Subscribe to my newsletter and join our growing community—we’ll create something magical together. I promise, it’ll never be boring!
Stay updated with the latest news—subscribe to our newsletter today!
Thank you all—wishing you an amazing day ahead!
Read more related Articles at InnoVirtuoso
- How to Completely Turn Off Google AI on Your Android Phone
- The Best AI Jokes of the Month: February Edition
- Introducing SpoofDPI: Bypassing Deep Packet Inspection
- Getting Started with shadps4: Your Guide to the PlayStation 4 Emulator
- Sophos Pricing in 2025: A Guide to Intercept X Endpoint Protection
- The Essential Requirements for Augmented Reality: A Comprehensive Guide
- Harvard: A Legacy of Achievements and a Path Towards the Future
- Unlocking the Secrets of Prompt Engineering: 5 Must-Read Books That Will Revolutionize You