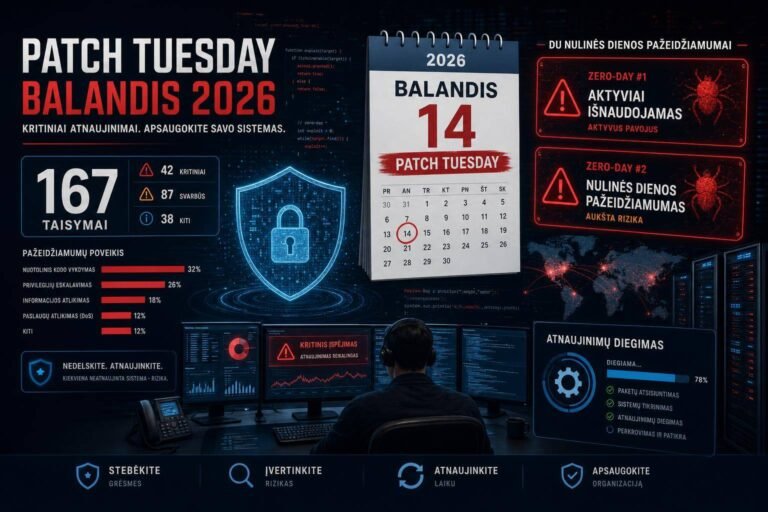
Microsoft Defender Reports Global Surge in Trojan.Win32/Surgent Malware Alerts: What Security Teams Must Do Now
Microsoft Defender users saw a flood of weekend alerts for Trojan.Win32/Surgent, a late-breaking Windows malware variant with data exfiltration and persistence capabilities. By Monday morning, many SOCs were staring at wall-to-wall detections, triage queues spiking, and a simple question from leadership: is this real, how bad is it, and what are we doing about it?
The answer depends on swift, disciplined response. Whether you’re dealing with a genuine outbreak, noisy telemetry, or a mix of both, the next 24–72 hours will determine impact. This guide translates the surge in Microsoft Defender alerts into an actionable playbook—what to verify, how to cut through alert noise, where to look for persistence and exfiltration, and how to shore up defenses while the dust settles.
We also cover concurrent vulnerability chatter around Linux, cPanel, SonicWall firewalls, and Wireshark—because attackers rarely operate in silos, and today’s malware alert spike can be tomorrow’s edge-device pivot if you neglect patching and segmentation.
Executive triage: what matters right now
When an emerging family like Trojan.Win32/Surgent triggers global alerts, defenders must balance speed with rigor. Aim for three outcomes in the first hours:
- Establish ground truth: Are detections tied to executed binaries or real user activity? Or are they scanning hits, blocked files, or quarantined artifacts without execution?
- Contain potential spread: Quarantine likely-compromised endpoints fast. Preserve forensic evidence before remediation.
- Stabilize operations: Clear false positives, de-duplicate related alerts, and prioritize the small subset of endpoints with signs of execution and outbound traffic.
A pragmatic 4-24-72 runbook:
- First 4 hours
- Confirm Defender is up to date across endpoints. Verify engine and signature versions and push emergency updates if lagging. See Microsoft’s documentation on Defender Antivirus security intelligence updates.
- Isolate endpoints with Defender alerts that also show process execution or egress traffic. Don’t isolate everything; prioritize based on execution and network signals.
- Stand up a focused detection lens in your SIEM or Microsoft 365 Defender Advanced Hunting for “Surgent” hits that include process and network context. Use the queries provided below as a starting point.
- First 24 hours
- Hunt for persistence and exfiltration behaviors (registry run keys, scheduled tasks, BITS jobs, suspicious PowerShell, Rclone/OneDrive/Cloud sync abuse, unusual DNS).
- Block known bad hashes/URLs/domains with your EDR/NDR stack and host firewall egress controls. In Microsoft 365 Defender, leverage custom indicators.
- Quarantine and reimage endpoints only after collecting triage artifacts. Avoid destroying evidence too early.
- First 72 hours
- Address patchable exposure on edge devices and tooling, including SonicWall, Wireshark, web hosting panels, and Linux servers (see vendor references below).
- Strengthen prevention: enforce Attack Surface Reduction (ASR) policies, tighten egress, and restrict unlabeled executables from running.
- Update detection content to reduce noise and catch variants (YARA-based detections, KQL refinements).
For incident handling process rigor, align actions to NIST’s proven guidance in the Computer Security Incident Handling Guide (SP 800-61r2), which covers preparation through post-incident lessons learned. Reference: NIST SP 800-61r2.
What is Trojan.Win32/Surgent? How Microsoft Defender sees the threat
Surgent is being flagged by Microsoft Defender as a Windows trojan with two headline capabilities: persistence (staying resident on systems across reboots) and data exfiltration (moving sensitive information off-network). Those are broad categories, but they map to common tradecraft defenders can hunt for:
- Persistence examples (MITRE ATT&CK: TA0003, e.g., Run Keys, Services, Scheduled Tasks)
- Exfiltration examples (MITRE ATT&CK: TA0010 Exfiltration, e.g., exfil over HTTPS, use of cloud storage APIs, DNS tunneling)
The surge in alerts suggests either: – Rapid deployment of a new detection signature catching previously unseen samples or delivery tooling; or – Active campaigns pushing Surgent at scale through common vectors (phish with attachments, drive-by downloads, cracked software bundles, supply chain droppers, or lateral movement from already-compromised nodes).
Because Defender’s detection family name surfaces across multiple telemetry layers (file detection, behavioral detections, script analysis), you can get a sudden spike even when most events are blocked or quarantined. Your mission is to separate executed, persistent, and beaconing instances from noisy background detections.
Rapid verification: update, hunt, and isolate
Before you assume the worst, make sure you can trust what Defender is telling you.
1) Verify Defender currency – Ensure endpoints have the latest platform, engine, and security intelligence. On Windows, a quick verification: – PowerShell: Get-MpComputerStatus | select AMProductVersion, AMServiceEnabled, AntispywareEnabled, AntivirusEnabled, NISSignatureVersion, AntispywareSignatureVersion – Update signatures: Update-MpSignature – Cross-check enterprise-wide versions through your EDR/endpoint management console. Microsoft’s official guidance on staying current is here: Defender AV updates.
2) Focused hunting for Surgent activity – Use Microsoft 365 Defender Advanced Hunting (KQL) to scope the blast radius and separate detections with execution context from simple file hits. Start with:
Find alerts that mention Surgent – AlertInfo | where Title has_any (“Surgent”, “Trojan.Win32/Surgent”) | summarize count() by Title, DetectionSource, bin(Timestamp, 1h)
Identify devices with Surgent alerts and suspicious process execution within a 2-hour window – let surgentDevices = AlertInfo | where Title has_any (“Surgent”, “Trojan.Win32/Surgent”) | summarize by DeviceId; DeviceProcessEvents | where DeviceId in (surgentDevices) | where Timestamp between (ago(48h) .. now()) | where ProcessCommandLine has_any (“curl”, “bitsadmin”, “powershell -enc”, “certutil”, “rclone”, “7z”, “winrar”, “python”, “wscript”, “mshta”) | project Timestamp, DeviceName, InitiatingProcessFileName, FileName, ProcessCommandLine, InitiatingProcessAccountDomain, InitiatingProcessAccountName
Highlight network egress from Surgent-alerted hosts – let surgentDevices = AlertInfo | where Title has_any (“Surgent”, “Trojan.Win32/Surgent”) | summarize by DeviceId; DeviceNetworkEvents | where DeviceId in (surgentDevices) | where Timestamp between (ago(48h) .. now()) | where RemotePort in (80, 443) and BytesSent > 5000000 | summarize TotalBytesSent = sum(BytesSent) by DeviceName, RemoteUrl, RemoteIP, bin(Timestamp, 1h) | top 50 by TotalBytesSent desc
3) Isolate with precision – Isolate endpoints that show both: – A Defender Surgent alert, and – Evidence of execution plus outbound traffic or persistence artifacts. – Avoid isolating every alerted machine without context; you’ll disrupt operations and lose credibility. Build a short list to quarantine, then collect forensic artifacts before reimage or cleanup.
For analysts new to hunting, Microsoft’s documentation on the Advanced Hunting Query Language is an excellent primer: Advanced Hunting KQL guide.
Persistence and exfiltration checks: where to look, what to capture
Surgent’s family classification points to two jobs: stick around and sneak data out. Here’s how to look for both effectively.
1) Persistence triage – Startup locations: Examine registry Run and RunOnce keys, Services, Scheduled Tasks, WMI Event Consumers, and Startup folders. – Tools: Sysinternals Autoruns (GUI or CLI) remains a gold standard for enumerating persistence; run it from a trusted admin workstation and save output for comparison. – Stomped timestamps or odd parent-child chains often indicate dropper activity. – Hunt examples: – DeviceRegistryEvents | where ActionType == “RegistryValueSet” and RegistryKey has_any (“Run”, “RunOnce”, “Services”) and InitiatingProcessFileName !in (“Explorer.exe”, “services.exe”) – DeviceProcessEvents | where FileName has_any (“schtasks.exe”, “powershell.exe”, “wmic.exe”) and ProcessCommandLine has_any (“/create”, “Register-WmiEvent”)
2) Exfiltration triage – Cloud service abuse: Look for unusual spikes to cloud storage endpoints (new OneDrive tenants, unfamiliar S3 buckets, uncommon WebDAV). – HTTPS or DNS: Exfil over encrypted channels is the norm; correlate increased egress (BytesSent) with suspicious processes. – Staging behavior: Temporary archives (ZIP/7z), shadow copies abuse, and compress-then-send patterns. – Hunt examples: – DeviceNetworkEvents | where RemoteUrl has_any (“drive.google.com”, “dropbox.com”, “api.onedrive.com”, “content.dropboxapi.com”, “s3.amazonaws.com”) and BytesSent > 5000000 – DeviceFileEvents | where FileName has_any (“.zip”, “.7z”) and InitiatingProcessFileName has_any (“cmd.exe”, “powershell.exe”) and FolderPath has_any (“\Users\*\AppData\Local\Temp”, “C:\Windows\Temp”)
3) Evidence collection – Before you remediate: – Capture volatile artifacts: process lists, network connections, ARP, DNS cache. – Copy suspected binaries, scripts, and scheduled task XMLs. – Export EDR timeline snippets (24–72 hours). – This positions you to confirm root cause, track operator behavior, and refine detections.
Ground your workflow in recognized incident response fundamentals. NIST SP 800-61r2 remains a concise baseline for containment, eradication, and recovery: NIST Computer Security Incident Handling Guide.
Emergency containment: steps that work in the real world
Containment must be fast, reversible, and minimally disruptive.
- Quarantine with fallbacks: Use your EDR’s isolation and remediate-in-place features, but keep a failsafe path (out-of-band management or on-site support) if remote isolation cuts you off.
- Block-by-default egress for quarantined segments: Create a restricted VLAN for suspect hosts with only update servers, EDR cloud, and IR tooling accessible.
- Turn on or tighten ASR: Microsoft’s Attack Surface Reduction rules can prevent common dropper and LOLBIN behaviors used for data theft. Prioritize rules that block Office from creating child processes, credential stealing from LSASS, and executable content from email/web downloads. Reference: Attack Surface Reduction (ASR) rules.
- Restrict script interpreters: Constrain PowerShell to Constrained Language Mode for non-admin users; log module and script block execution. Lock down wscript/cscript, mshta, and living-off-the-land binaries.
- Temporary domain blocks: If you have indicators from your TI team, deploy temporary DNS and proxy blocks for known C2 or exfil endpoints, while you validate impact.
- Preserve business continuity: For endpoints running critical workloads, prefer network containment and controlled remediation over immediate reimage—after capturing evidence.
Cleaning up Windows endpoints safely
After you’ve contained the spread and gathered evidence, move through controlled eradication:
1) Update and full scan – Ensure Defender signatures and platform are up to date enterprise-wide. – Run targeted scans first to reduce resource impact, then schedule rolling full scans for non-critical hours. – For systems with confirmed execution, consider a Defender Offline scan or equivalent boot-time scanning approach when operationally feasible.
2) Persistence removal – Use EDR remediation to remove registry entries, tasks, and services. Manually validate with Autoruns or equivalent. – Clear dropper artifacts in temp directories and user profile paths, confirming with EDR telemetry that no re-creation occurs post-reboot.
3) Reimage when in doubt – If you can’t confidently verify removal (e.g., suspicious kernel-mode drivers, deeply embedded persistence), reimage from a known-good, patched baseline. – Rotate credentials touched by the compromised endpoint (local admin, service accounts, cached credentials).
4) Post-cleanup validation – Monitor the endpoint for 24–72 hours with enhanced telemetry filters for re-infection signals (new tasks, outbound spikes, unusual DNS patterns).
Don’t ignore the rest of the stack: patch Linux, cPanel, SonicWall, and Wireshark
Weekend malware surges often coincide with opportunistic exploitation of widely used infrastructure. Even if Surgent targets Windows, adversaries pivot through vulnerable third-party tools and edge devices.
- SonicWall firewalls: Check your versions and review the latest PSIRT advisories and hotfixes. Harden management interfaces and disable legacy access where possible. Reference: SonicWall PSIRT vulnerability list.
- Wireshark: Popular on analyst and admin workstations, Wireshark’s dissectors occasionally have critical parsing bugs. Running outdated builds on investigative endpoints is risky. Keep current with the official security page: Wireshark Security Advisories.
- cPanel: Hosting panels are frequent targets for brute force, plugin abuse, and unpatched core flaws. Audit exposed management endpoints, enforce MFA, and keep to the latest TSR/security releases. Reference: cPanel Security Advisories.
Treat these as separate but connected risk channels. A Microsoft Defender alert wave on endpoints plus an out-of-date firewall or management panel is a recipe for lateral movement and reinfection.
Detection engineering: tuning for signal, not noise
To manage a global alert surge, refine detections while you contain:
- Group and de-duplicate alerts:
- Aggregate by device, process hash, and initiating parent to reduce alert storm duplicates.
- Add correlation rules that promote alerts to incidents only when combined with execution and outbound connections.
- Expand beyond hash-based indicators:
- Behavior > signatures. Watch for suspicious process chains (Office -> PowerShell -> curl), archive creation prior to egress, and BITS/Certutil misuse.
- Leverage pattern-based detections in EDR and SIEM.
- Apply time-window correlation:
- Detections clustered in a 10–30 minute window often indicate an execution chain. Promote those incidents; deprioritize isolated single-file hits with no follow-on behavior.
- Update EDR exclusions cautiously:
- Don’t disable core protections or add broad exclusions to quiet alerts without a second control confirming benign behavior.
- Document temporary tuning and set expiry dates for every exception.
- Use Microsoft 365 Defender Advanced Hunting custom detections:
- Convert stable hunting queries into scheduled rules that create incidents when behavior+egress conditions co-occur.
- Map to MITRE ATT&CK to ensure coverage for exfiltration behaviors like those under TA0010.
Governance and communication: keeping leadership informed without causing panic
A Monday morning swarm of “Trojan” alerts is politically charged. Keep communications crisp:
- Risk statement (non-technical): We are seeing elevated Microsoft Defender detections for a Windows trojan known as Surgent. We are verifying which alerts reflect execution versus blocked files. A small subset of systems shows signs of activity; those are being isolated and remediated.
- Impact to operations: Some users may experience short-term isolation or scanning slowdowns. Core business systems remain operational.
- Concrete actions taken: Signature updates completed, targeted isolation in progress, hunts for persistence and data egress running, edge patch checks underway (SonicWall, Wireshark, cPanel).
- Next updates: Provide predictable cadences (e.g., top-of-hour for first half-day, then every 4 hours).
Align these updates to a formal incident lifecycle so they’re anchored in process, not improvisation. CISA’s playbooks for cybersecurity incidents are a useful external reference for structure and roles: Federal Government Cybersecurity Incident and Vulnerability Response Playbooks.
Hardening checklist to reduce Surgent-like risk
Prioritize quick wins while incident response unfolds:
- Prevention
- Enforce ASR rules most relevant to dropper behaviors and credential access: Attack Surface Reduction rules.
- Disable or restrict legacy scripting engines; prefer signed PowerShell with enterprise logging.
- Implement WDAC or AppLocker for high-risk user groups.
- Credential hygiene
- Deploy LAPS for local admin rotation.
- Remove local admin from standard users; enforce MFA for remote access and management consoles.
- Egress controls
- Default-deny outbound for sensitive segments; allow-list only required SaaS APIs.
- Deploy DNS logging and response policy zones to block newly registered or known malicious domains.
- Monitoring and logging
- Enable script block logging, process command-line logging, and detailed PowerShell transcription.
- Centralize logs; maintain at least 30–90 days of searchable telemetry.
- Patch and configuration management
- Patch Wireshark and other admin tools promptly.
- Check SonicWall and cPanel against current advisories.
- Tighten exposure of management interfaces to VPN or jump hosts only.
- Incident readiness
- Keep an endpoint triage toolkit ready: EDR collectors, memory acquisition, and persistence enumerators.
- Pre-approve isolation and emergency changes to avoid change-control delays during containment.
Common mistakes to avoid during a malware alert surge
- Nuking first, asking later: Reimaging without collecting artifacts kills your ability to understand root cause, and you’ll miss attacker tradecraft needed to prevent recurrence.
- Trusting a single signal: A file detection alone is not an incident. Combine with execution and network evidence.
- Disabling protections to quiet alerts: Temporary relief that invites a real breach.
- Ignoring non-Windows layers: If your SonicWall, Wireshark, or cPanel stack is outdated, an endpoint compromise can turn into a network foothold.
- Failing to verify backups: During volatile events, validate that backups are intact and test restores. Assume ransomware operators watch for chaos.
Example tools and commands for Windows defenders
- Defender status and updates (run as admin)
- Get-MpComputerStatus | fl AMProductVersion,AMEngineVersion,AntivirusSignatureVersion
- Update-MpSignature
- Quick suspicious activity checks
- Get-ScheduledTask | where {$_.TaskName -match “(?i)(update|win|diag|service)”} | Format-List
- Get-WinEvent -FilterHashtable @{LogName=‘Microsoft-Windows-PowerShell/Operational’; StartTime=(Get-Date).AddDays(-2)} | Select TimeCreated,Id,Message
- Forensic capture reminders
- Copy suspect binaries and scripts from user temp and startup paths.
- Export scheduled tasks (schtasks /query /tn “TaskName” /xml).
While Sysinternals Autoruns is near-essential for persistence discovery, run it from a trusted admin workstation and export CSV/ARN files for comparison after cleanup.
Advanced hunting: building durable detections
Turn your reactive searches into proactive detections:
- Promote hunts with a confidence threshold:
- Require the presence of high-signal behaviors like compress-then-exfiltrate, or Office -> PowerShell -> curl chains, before alerting.
- Add allow-lists for known IT tools:
- If Rclone is used legitimately, require signed binaries, expected command-line patterns, or execution only on IT-admin profiles.
- Integrate with ticketing:
- Create incident records with device, user, and process context automatically, so analysts aren’t copying KQL results manually.
For reference and syntax nuance, keep Microsoft’s KQL guide handy: Advanced Hunting query language.
FAQ
What is Trojan.Win32/Surgent? – A Windows trojan family flagged by Microsoft Defender with capabilities tied to persistence and data exfiltration. It typically requires user or system execution and then attempts to stay resident and move data off the machine.
Are the recent Microsoft Defender Surgent alerts false positives? – Not necessarily. A surge can indicate broader detection coverage or increased attacker activity. Validate by looking for execution context (process events) and outbound connections from alerted hosts. Treat isolated file detections differently from executed malware.
How do I update Microsoft Defender signatures across endpoints quickly? – Ensure your endpoint management solution forces an immediate signature and platform update. Locally, use Update-MpSignature and verify with Get-MpComputerStatus. Enterprise guidance: Defender Antivirus updates.
What’s the fastest way to check for data exfiltration from a host? – Correlate Defender alerts with DeviceNetworkEvents showing large BytesSent over HTTPS, especially to unfamiliar cloud storage domains. Look for recent archive creation (ZIP/7z) in temp directories and suspicious tool usage (curl, certutil, BITS, Rclone).
Should I reimage every endpoint with a Surgent alert? – No. Isolate first, collect evidence, then decide. Reimage confirmed-compromised systems or those with uncertain cleanup. For blocked-only detections with no execution or persistence, remediation-in-place may be sufficient.
Do I need to patch tools like Wireshark or edge devices like SonicWall during this event? – Yes. Attackers chain weaknesses. Out-of-date admin tools and edge devices are common pivot points. Check vendor advisories for urgent updates: Wireshark security advisories and SonicWall PSIRT. If you manage cPanel environments, review current notices: cPanel Security Advisories.
The bottom line
A global surge in Microsoft Defender alerts for Trojan.Win32/Surgent is exactly the kind of event that strains SOCs and tests incident response discipline. The winning formula is clear: verify Defender currency, hunt decisively for execution plus egress, isolate with precision, and remediate without erasing your forensic trail. In parallel, harden Windows with ASR, restrict egress, and close exposure on critical adjacent systems like SonicWall, Wireshark, and cPanel.
Anchor your response in proven frameworks, automate what you learn into durable detections, and document everything. The organizations that use a Surgent-scale scare to improve their prevention, detection, and recovery posture will ride out not just this wave—but the next one.
If you’re staring at a queue full of Trojan.Win32/Surgent alerts right now, start with updates, targeted isolation, and the hunts above. Then turn today’s incident into tomorrow’s resilience.
Discover more at InnoVirtuoso.com
I would love some feedback on my writing so if you have any, please don’t hesitate to leave a comment around here or in any platforms that is convenient for you.
For more on tech and other topics, explore InnoVirtuoso.com anytime. Subscribe to my newsletter and join our growing community—we’ll create something magical together. I promise, it’ll never be boring!
Stay updated with the latest news—subscribe to our newsletter today!
Thank you all—wishing you an amazing day ahead!
Read more related Articles at InnoVirtuoso
- How to Completely Turn Off Google AI on Your Android Phone
- The Best AI Jokes of the Month: February Edition
- Introducing SpoofDPI: Bypassing Deep Packet Inspection
- Getting Started with shadps4: Your Guide to the PlayStation 4 Emulator
- Sophos Pricing in 2025: A Guide to Intercept X Endpoint Protection
- The Essential Requirements for Augmented Reality: A Comprehensive Guide
- Harvard: A Legacy of Achievements and a Path Towards the Future
- Unlocking the Secrets of Prompt Engineering: 5 Must-Read Books That Will Revolutionize You