Shadow IT, Explained: The Hidden Risk of Unauthorized Tools (and How to Stop It Without Killing Productivity)
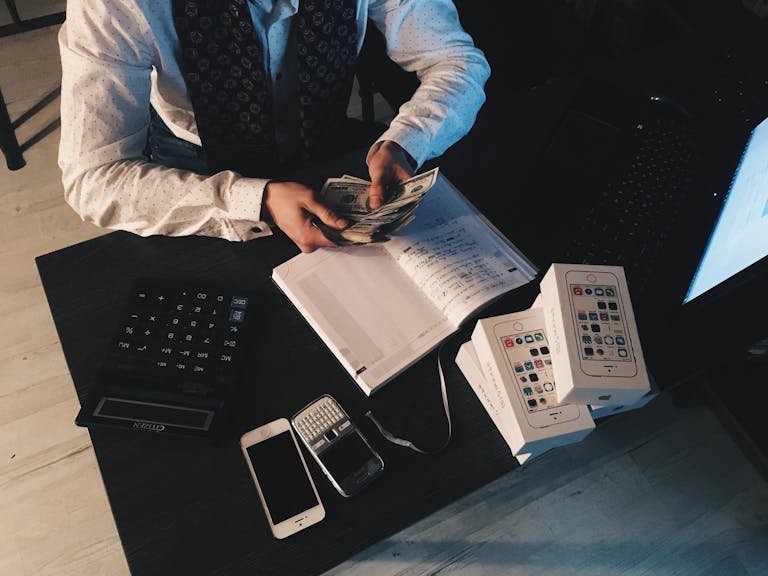
If you’ve ever spun up a quick Google Sheet, tried a free project tool, or used your personal phone to grab a work file “just this once,” you’ve touched Shadow IT. It’s the software, cloud services, and devices employees use without IT’s approval. It feels helpful in the moment. It’s fast. It gets work done….