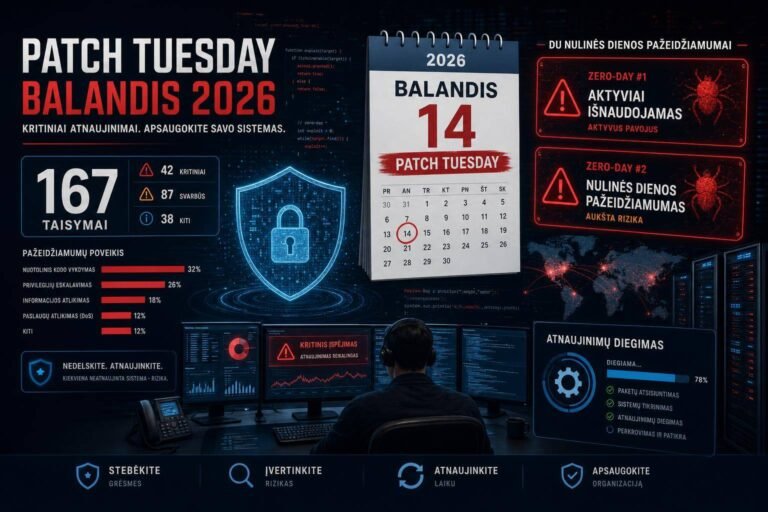
Microsoft April 2026 Patch Tuesday: 167 Vulnerabilities Fixed, Two Zero-Days Demand Immediate Action
Microsoft’s April 2026 Patch Tuesday lands with a heavy lift: 167 vulnerabilities fixed across the ecosystem and two zero-days in the mix—one actively exploited and one publicly disclosed. For enterprise defenders, the signal is clear: prioritize rollout, verify Microsoft Defender platform coverage, and harden SharePoint environments without delay.
This cycle matters because the zero-days hit two high-value layers many organizations rely on every day: Microsoft SharePoint Server (active exploitation) and Microsoft Defender (public disclosure, system-level privilege). The combined risk profile increases the chance of chained attacks that start with social engineering or web-layer abuse and quickly escalate to full-system control.
Below, you’ll find a focused breakdown of the zero-days, a practical 72-hour response playbook, step-by-step verification for the Defender fix, SharePoint hardening guidance, and the governance practices that keep patch velocity high and risk low.
What’s in April 2026 Patch Tuesday
Microsoft’s April 2026 release addresses 167 vulnerabilities spanning Microsoft’s enterprise stack. While the exact product breakdown isn’t the headline, two zero-days are:
- CVE-2026-32201 (SharePoint Server spoofing; actively exploited)
- CVE-2026-33825 (Microsoft Defender elevation of privilege; publicly disclosed, fix auto-delivered via platform update 4.18.26030.3011)
Microsoft distinguishes zero-days as vulnerabilities that are publicly disclosed or actively exploited before a fix is broadly available. You’ll find authoritative details and CVE pages in the Microsoft Security Update Guide, and you should reference CVSS to calibrate severity and potential blast radius alongside business context (NIST CVSS overview).
Two zero-days in the same cycle often point to elevated threat activity or attacker focus on Microsoft infrastructure. Whether that stems from increased bug-hunting or adversary tempo, the operational takeaway is the same: accelerate prioritization and patching, and monitor for anomalous behavior in your collaboration tier and endpoint fleet.
The zero-days that matter now
CVE-2026-32201 — SharePoint Server spoofing (actively exploited)
- Category: Spoofing due to improper input validation
- Risk: Attackers can abuse how SharePoint handles user input to make content appear trustworthy or originate from a legitimate source. That can amplify phishing, session hijacking attempts, or credential harvesting within intranets and extranets.
- Exposure: Any SharePoint Server accessible to users—especially internet-facing portals, vendor extranets, and hybrid deployments—should be prioritized.
While Microsoft has not disclosed exploitation specifics, the vulnerability class suggests attackers could coerce clicks, mask malicious content as trusted pages or components, or manipulate parameters such that users (or services) accept falsified context. In collaboration platforms, “looking legitimate” is often enough to trigger bad decisions. That’s why robust input validation is a cornerstone of secure web apps; guidance from OWASP on validation and encoding remains a useful mental model (OWASP Input Validation Cheat Sheet).
Operationally, treat this as a high-likelihood phishing and social-engineering amplifier with potential for lateral movement if credentials or tokens are captured. Patch your SharePoint servers early in the cycle and increase monitoring for unusual access, parameter manipulation, and atypical page behaviors.
CVE-2026-33825 — Microsoft Defender elevation of privilege (publicly disclosed)
- Category: Local elevation of privilege to SYSTEM
- Fix: Delivered via Microsoft Defender Antimalware Platform update 4.18.26030.3011
- Deployment: Auto-download to affected systems; verify fleet coverage
A local privilege escalation (LPE) in Microsoft Defender is a force multiplier for attackers who already have code execution (e.g., via a macro, vulnerable driver, or living-off-the-land techniques). By achieving SYSTEM, adversaries can disable security tools, dump credentials, establish persistence, or manipulate the OS with maximum privileges. The good news: the fix is shipped through Defender’s platform update mechanism, which typically auto-deploys. The caution: coverage gaps frequently exist for devices that are offline, isolated, misconfigured, VDI gold images, or stuck behind update controls.
Track this CVE in your “must-verify” list. Don’t assume auto-update equals complete coverage—prove it with version checks and compliance reporting. To align prioritization with threat reality, keep an eye on the CISA Known Exploited Vulnerabilities catalog and update your patch SLAs if these CVEs appear there.
Who is most at risk right now?
- Organizations with SharePoint Server exposed to the internet (even partially), third-party contractors, or unmanaged partner access.
- Enterprises that rely on standard Defender update channels but have VMs, VDI images, lab environments, or remote endpoints that intermittently miss updates.
- Environments with limited segmentation where a compromised SharePoint user can quickly access sensitive applications or data shares.
- Teams without strong change control or who delay patching collaboration servers due to uptime concerns.
For these profiles, the combination of spoofing in a collaboration tier and local EoP on endpoints raises the probability of short, effective attack chains: lure a user via SharePoint content, obtain a foothold, escalate with Defender LPE, then pivot.
A 72-hour prioritization playbook
Use this sprint plan to reduce time-to-remediation without sacrificing control.
Day 0: Rapid triage and scoping
- Build a quick asset view – Inventory all SharePoint Server instances. Note exposure (internet-facing vs. internal), role (portal, extranet, BI, app hosting), and business criticality. – Inventory devices with Microsoft Defender as the primary AV (Windows client and server).
- Establish patching channels – Confirm your patch sources (Windows Update for Business, WSUS, ConfigMgr/Intune). – Validate that Defender platform updates are not blocked by policy. – If you manage updates via rings, confirm critical servers are in accelerated rings (Windows Update for Business overview).
- Validate Defender platform version coverage – See the implementation section below for exact commands. – Flag outliers: offline devices, VDI bases, images not refreshed this quarter, and endpoints in restricted networks.
- Risk-based sequencing – First: Internet-facing SharePoint servers. – Second: High-privilege SharePoint farms hosting sensitive content (HR, finance, M&A). – Third: Core Windows server tiers and user endpoints—ensure Defender platform update version 4.18.26030.3011 is present.
Day 1: Patch, verify, and observe
- Apply SharePoint updates to staging, run smoke tests (authentication, search, workflow, web parts, BI components), then promote to production during a controlled window.
- Force Defender platform updates on endpoints that missed auto-deployment by triggering an update cycle via Intune/ConfigMgr or command line.
- Validate telemetry: confirm event collection is healthy; enable extra auditing for SharePoint and endpoint security during the rollout period.
Day 2: Close gaps and add compensating controls
- Mop-up stragglers. Any SharePoint instance or endpoint still missing the update becomes a ticketed incident with executive visibility.
- Enable or tighten guardrails:
- Attack Surface Reduction (ASR) rules where feasible on endpoints to reduce script- and macro-based abuse (Manage Microsoft Defender Antivirus updates and platform).
- Strengthen reverse proxies/WAF rules for SharePoint to block suspicious query strings and enforce strict header policies.
- Review conditional access rules for SharePoint; require MFA for sensitive sites, consider device-compliance gating.
Day 3: Validate resiliency
- Confirm backups and recovery plans for SharePoint farms are recent and tested.
- Run a targeted threat hunt for anomalous SharePoint access and signs of post-exploitation (see detection section).
- Close the loop with change records, coverage reports, and a short post-action review.
Implementation details: verify Microsoft Defender platform 4.18.26030.3011
Even though Microsoft states the fix is delivered automatically, mature teams verify.
- Local check via PowerShell on Windows:
- Open an elevated PowerShell prompt.
- Run: Get-MpComputerStatus | Select AMProductVersion
- Confirm AMProductVersion includes 4.18.26030.3011 (or later if superseded).
- Cmdlet reference: Get-MpComputerStatus documentation
- Remote fleet verification:
- Use your endpoint management tool (Intune/ConfigMgr) to query AMProductVersion across devices.
- Segment by device group (laptops, servers, VDI, kiosks) to find systemic gaps.
- Update channels and nudging:
- Ensure Microsoft Defender Antivirus updates for security intelligence, platform, and engine are enabled for your managed endpoints.
- If necessary, temporarily relax deferral policies to ingest the platform update promptly.
- Reference: Maintain and manage Microsoft Defender Antivirus updates
- Special cases:
- VDI master images need manual refresh, then recompose pools.
- Offline or isolated networks require importing the platform update through approved transfer methods and local deployment tools.
- Servers with third-party AV still benefit if Defender is in passive or EDR block mode; verify the platform update regardless of active role.
SharePoint Server hardening and monitoring (until fully patched)
Patching is step one; hardening and observability reduce risk if attackers attempt to exploit lagging systems or test residual weaknesses.
- Apply Microsoft’s latest guidance on server hardening, TLS, service accounts, and isolation: Security hardening for SharePoint Server
- Restrict or temporarily disable custom web parts and user-provided scripts on high-risk sites if business permits.
- Normalize and sanitize input wherever customizations exist. Avoid direct rendering of unsanitized HTML or query parameters.
- Enforce strict HTTP headers at your reverse proxy:
- Content-Security-Policy to limit script sources.
- X-Content-Type-Options: nosniff.
- X-Frame-Options or frame-ancestors directives to prevent clickjacking.
- Use a WAF to block or alert on:
- Suspicious query strings, unusual encoding, or malformed parameters.
- Repeated requests from single IPs that target specific SharePoint endpoints.
- Increase SharePoint auditing and Unified Logging Service (ULS) verbosity during the patch window to support triage.
- Segmentation and conditional access:
- Limit admin consoles to jump hosts.
- Require MFA for site owners and administrators.
- Consider device-compliant-only access for privileged sites.
Detection and threat hunting ideas
You don’t need perfect signatures to spot trouble. Combine behavioral clues across endpoints and SharePoint.
- SharePoint signals
- Spikes in failed authentication followed by immediate success from the same IP or user.
- Unusual creation or modification of pages with embedded scripts.
- Atypical parameter patterns in URLs, or repeated access to specific pages that handle inputs.
- Endpoint signals (post-exploitation patterns)
- New or unexpected services installed soon after user interaction with SharePoint.
- Command shells or scripting engines launched by Office products or browsers.
- Security control tampering: disabling services, altering registry keys related to Defender.
If you use Microsoft Defender for Endpoint, leverage advanced hunting to stitch events across host and identity. Start with process trees that include browser-to-script-to-admin-tool patterns, and look for escalation attempts after SharePoint interactions. Reference: Microsoft Defender for Endpoint advanced hunting
If your SOC maps detections to MITRE ATT&CK, focus on techniques commonly used with these classes of bugs: exploiting public-facing applications (initial access) and local privilege escalation. Correlate with identity telemetry to spot suspicious role changes or token anomalies.
Governance and SLAs: make the sprint repeatable
Rapid, reliable patching isn’t just tooling—it’s a governance habit.
- Set SLAs by severity and exposure:
- Internet-facing critical: 48–72 hours.
- Privileged infrastructure: 7 days.
- General endpoints: 14 days (faster for zero-days).
- Use a risk-based framework grounded in industry guidance like NIST SP 800-40 Rev. 3: Guide to Enterprise Patch Management.
- Calibrate prioritization using authoritative sources:
- Act quickly on entries that appear in the CISA KEV catalog.
- Bake verification into the process:
- Require post-patch evidence (version checks, health signals).
- Track exceptions and compensating controls with clear owners and deadlines.
- Keep change control lean:
- Maintain preapproved emergency windows for zero-days.
- Use phased rings with automated rollback if telemetry degrades.
Common mistakes to avoid this Patch Tuesday
- Assuming Defender’s auto-update covered every device without checking AMProductVersion.
- Deferring SharePoint patches because “it’s only internal.” Spoofing and phishing risks don’t respect intranet boundaries.
- Patching endpoints but skipping management tiers (jump hosts, RDP gateways, admin workstations) where attacker ROI is highest.
- Ignoring VDI and gold images; failing to recompose means persistent gaps.
- Skipping reboots where required, leaving binaries loaded in memory and protections incomplete.
- Neglecting compensating controls (ASR rules, WAF policies, conditional access) while change approvals queue up.
Practical checklist: from decision to done
- Review Microsoft’s April 2026 release in the Security Update Guide.
- Sequence targets:
- Internet-facing SharePoint → sensitive SharePoint farms → core servers → endpoints.
- Verify Defender platform version 4.18.26030.3011+ across devices using Get-MpComputerStatus and your device management platform.
- Accelerate update rings and temporarily relax deferrals for critical segments (Windows Update for Business overview).
- Apply SharePoint patches, validate business-critical workflows, and enable enhanced logging during rollout.
- Implement compensating controls (WAF rules, CSP headers, ASR rules) and enforce MFA/conditional access for privileged users.
- Hunt for anomalies in SharePoint access and endpoint behaviors; correlate telemetry via your SIEM or Defender advanced hunting.
- Close exceptions with time-bound remediation plans; report coverage and residual risk to stakeholders.
- Fold lessons learned into your standard zero-day playbook aligned with NIST SP 800-40.
FAQ
What are the two zero-days fixed in Microsoft’s April 2026 Patch Tuesday?
CVE-2026-32201 is a SharePoint Server spoofing vulnerability that’s actively exploited. CVE-2026-33825 is a Microsoft Defender elevation of privilege vulnerability that was publicly disclosed and is fixed via Defender platform update 4.18.26030.3011.
How do I confirm my systems have the Defender fix?
On Windows, run Get-MpComputerStatus and check AMProductVersion. For environment-wide checks, query via Intune/ConfigMgr or your configuration management tool and confirm version 4.18.26030.3011 or later is present.
Which systems should I patch first?
Prioritize internet-facing SharePoint servers, then high-value SharePoint farms, then core infrastructure and endpoints—especially those used by admins. Ensure Defender platform coverage closes quickly across all device groups.
Are compensating controls necessary if I patch right away?
Yes. Even with patches applied, layered defenses (WAF rules, content security policies, ASR rules, MFA/conditional access) reduce residual risk, catch missed assets, and improve resiliency against new exploit variants.
Will updating Microsoft Defender cause downtime?
Defender platform updates are typically non-disruptive and auto-applied, but some environments with strict controls or offline devices require manual steps. Incorporate verification and, if needed, maintenance windows for servers with tight SLAs.
How do I monitor for exploitation attempts against SharePoint?
Increase auditing and ULS logging, watch for suspicious parameterized requests, page modifications with embedded scripts, and login patterns that transition quickly from failures to success. Correlate with endpoint telemetry for post-exploitation behaviors.
Conclusion: Move fast, verify coverage, and harden the edges
Microsoft’s April 2026 Patch Tuesday closes 167 vulnerabilities, with two zero-days that sharpen enterprise risk: an actively exploited SharePoint spoofing flaw (CVE-2026-32201) and a publicly disclosed Microsoft Defender elevation of privilege (CVE-2026-33825). The right response is decisive and methodical—patch SharePoint first where exposure is highest, verify Defender’s platform version across your fleet, and use compensating controls to contain any lingering gaps.
Treat this as a drill for your zero-day muscle memory. Anchor your process in authoritative guidance (Microsoft’s Security Update Guide, NIST’s patch management practices) and keep one eye on the CISA KEV catalog. When the next cycle lands, the teams that measure coverage, bake in hardening, and automate verification will be the ones sleeping soundly.
Discover more at InnoVirtuoso.com
I would love some feedback on my writing so if you have any, please don’t hesitate to leave a comment around here or in any platforms that is convenient for you.
For more on tech and other topics, explore InnoVirtuoso.com anytime. Subscribe to my newsletter and join our growing community—we’ll create something magical together. I promise, it’ll never be boring!
Stay updated with the latest news—subscribe to our newsletter today!
Thank you all—wishing you an amazing day ahead!
Read more related Articles at InnoVirtuoso
- How to Completely Turn Off Google AI on Your Android Phone
- The Best AI Jokes of the Month: February Edition
- Introducing SpoofDPI: Bypassing Deep Packet Inspection
- Getting Started with shadps4: Your Guide to the PlayStation 4 Emulator
- Sophos Pricing in 2025: A Guide to Intercept X Endpoint Protection
- The Essential Requirements for Augmented Reality: A Comprehensive Guide
- Harvard: A Legacy of Achievements and a Path Towards the Future
- Unlocking the Secrets of Prompt Engineering: 5 Must-Read Books That Will Revolutionize You