May 5, 2026 Cybersecurity Roundup: Email Security Alliances and a Healthcare Ransomware Wake-Up Call
If you only skim one cybersecurity brief this week, make it this one. Three threads from May 5’s news point to the same story: attackers still love email, defenders are teaming up to close gaps, and when ransomware hits critical industries, the blast radius goes way beyond IT. Let’s unpack what happened, why it matters, and what you should do before the next phishing lure or supply chain slip puts your operations at risk.
This analysis draws on the May 5, 2026 daily roundup from Osterman Research, which highlighted: – A new channel partner program from Sublime Security aimed at scaling email threat defense. – A KnowBe4–EasyDMARC partnership integrating DMARC enforcement with security awareness. – Donoma’s analysis of a ransomware incident at medical device maker Stryker, with operational disruption and possible exposure risks related to healthcare IoT and supply chains.
Below, you’ll find the signal behind the headlines, a practical action plan, and a board-ready narrative you can use today.
The signal behind the headlines
- Email is still the easiest door to kick in. Social engineering and spoofed domains continue to bypass tech-only controls. Two vendor moves on the same day—Sublime’s channel push and KnowBe4’s DMARC-aligned partnership—underline how defenders are pairing controls with behavior change.
- Ecosystem beats point products. The KnowBe4–EasyDMARC integration reflects a broader shift toward connecting identity, policy, and user training. Buyers want outcomes (fewer successful phishes, fewer spoofed emails), not just tools.
- Ransomware is an operational risk, not just an IT event. Donoma’s breakdown of the Stryker compromise shows how exploited vulnerabilities can cascade through IoT and supply chains into production halts—exactly where cyber meets P&L and patient safety.
Why email remains the front door
Email’s persistence as the primary initial access vector isn’t news—but the why matters: – Humans are adaptive… and so are attackers. Phishing kits mimic MFA prompts, trusted brands, and internal workflows with uncanny fidelity. – Authentication gaps persist. Without strong DMARC enforcement at p=reject and aligned SPF/DKIM, brand spoofing stays cheap and effective. – Business email compromise (BEC) evolves. It’s not just fake invoices; it’s supplier-side compromises, deepfake audio, and reply-chain hijacks.
The lesson: defenders need layered, mutually reinforcing controls—domain authentication, anomaly detection, and ongoing user conditioning—backed by fast incident response.
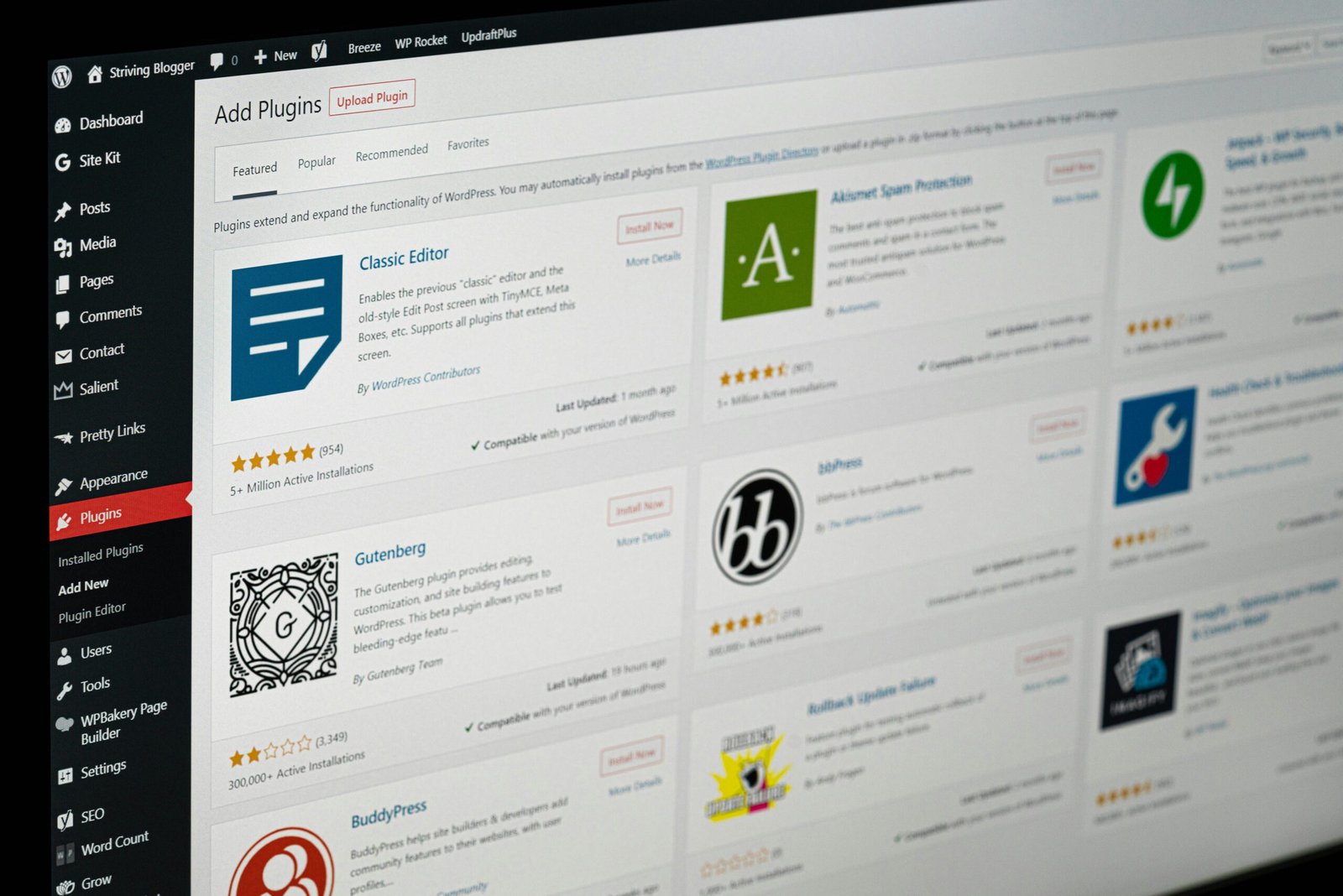
Sublime Security bets on the channel to scale email defense
Osterman reports that Sublime Security launched a channel partner program to expand adoption of its email security platform amid rising phishing threats.
What launched and why it matters
- Channel-first motions accelerate reach. With MSPs and MSSPs on board, mid-market and regional enterprises get access to modern email detection and response without standing up new teams.
- Email security needs context. Partners who manage endpoint, identity, and network telemetry can correlate signals, improving detection speed and precision.
- Buyers get choice. Channel ecosystems often pair technology with managed detection and response (MDR) and incident support, which many organizations now prefer over DIY stack assembly.
Explore Sublime Security’s platform and ecosystem: Sublime Security
How channel programs change buyer outcomes
- Faster time-to-value through prebuilt playbooks and deployment patterns.
- Integrated reporting across customers for benchmarked baselines (e.g., phishing catch rates, payload trends).
- 24/7 coverage that’s hard to replicate in-house for small security teams.
Questions to ask your MSP/MSSP now
- How do you tune detections for our unique communication patterns (VIPs, finance workflows, vendor domains)?
- What is your average time to quarantine post-detection and mean time to resolution (MTTR) for email threats?
- How do you integrate with our identity provider to spot anomalous login behavior linked to email-borne compromise?
- What’s your process for simulating targeted attacks (invoice fraud, supplier spoofing) and feeding lessons into user training?
KnowBe4 + EasyDMARC: closing the loop from policy to people
According to Osterman’s roundup, KnowBe4 and EasyDMARC are partnering to integrate DMARC enforcement with security awareness training—bringing domain authentication and human-layer defense under one umbrella.
Why this is a smart pairing
- DMARC reduces the noise. Enforcing DMARC at p=reject blocks a flood of direct-domain spoofing attempts before they reach users.
- Training sharpens the signal. Users are more likely to catch lookalike or compromised-supplier attacks if they’re regularly conditioned on emerging lures.
- Feedback loops reduce risk. When training data (e.g., click rates, reported phishes) informs authentication policy tuning and vice versa, organizations get fewer bypasses and faster detection of real threats.
DMARC enforcement matters—here’s the short version
- SPF and DKIM authenticate senders; DMARC tells receivers what to do if checks fail.
- Without DMARC enforcement, your domain can be impersonated at scale, eroding trust with customers and employees.
- Going from p=none to p=quarantine and then p=reject requires alignment work, but it’s achievable with staged reporting and monitoring.
Implementation steps for domain owners
- Inventory all legitimate sending sources (marketing, CRM, ticketing, payroll).
- Align SPF/DKIM for each source; minimize SPF flattening and record bloat.
- Start DMARC at p=none with reporting (rua/ruf) and iterate on alignment until failures are expected noise.
- Move to p=quarantine, monitor, then to p=reject for full protection.
- Integrate awareness training so users can still spot lookalike domains and compromised suppliers not blocked by DMARC.
Donoma’s take on the Stryker ransomware incident
Per Osterman’s summary, Donoma published analysis of a compromise affecting Stryker, a major medical device manufacturer. The incident reportedly involved ransomware, operational disruption, and patient data exposure risks tied to healthcare IoT and supply chains. While specifics may evolve as investigations proceed, the contours fit a familiar but serious pattern.
What reportedly happened
- Threat actors deployed ransomware within Stryker’s environment, disrupting operations.
- Initial access involved exploited vulnerabilities—suggesting unpatched systems, misconfigurations, or internet-exposed services as potential gateways.
- The fallout included production impacts and heightened concerns about sensitive data exposure, given the nature of medical device ecosystems and their data flows.
Attribution and technical details can change as forensics progress, but the operational story is consistent with recent sector incidents.
The healthcare IoT and supply chain angle
- Device sprawl expands the attack surface. Testing rigs, manufacturing systems, and connected devices often run legacy OS versions and bespoke firmware that are hard to patch quickly.
- Supplier access is a double-edged sword. Integrations that accelerate production can also provide lateral movement paths if partners are compromised.
- Production is time-critical. Even short halts can cascade through logistics, regulatory timelines, and hospital deployments—raising both financial and patient-care risks.
Operational fallout and resilience lessons
- Ransomware is a business continuity event. Backups matter, but so do tested restoration runbooks and pre-approved downtime protocols for critical lines.
- Visibility is the differentiator. OT/IoT assets require tailored monitoring—standard EDR isn’t enough for devices that can’t run agents.
- Segmentation buys time. Properly segmented environments constrain lateral movement, making containment and recovery faster.
Incident response playbook refreshers
- Triage with clear roles: threat intel, forensics, legal, communications, and executive liaison.
- Evidence preservation and chain-of-custody must be balanced with business restoration priorities.
- Communicate early and factually with stakeholders—regulators, customers, and partners—without speculating beyond what the investigation supports.
- Post-incident, quantify impacts and codify hard-won lessons into technical debt paydown and control uplift.
What these moves say about the security market in 2026
- Convergence is accelerating. Identity, email, endpoint, and data controls are consolidating via integrations and channel-delivered services.
- Outcomes > features. Buyers judge platforms on incident rates, dwell time, and recovery speed, not feature checklists alone.
- Partner ecosystems are a moat. Vendors that enable MSPs/MSSPs to deliver tailored, measurable outcomes will outpace solo point tools.
- Sector depth is a must. Healthcare, manufacturing, and energy require domain-specific telemetry, threat models, and compliance fluency.
Actionable checklist: next 30/60/90 days
30 days – Audit email exposure: – Verify DMARC policy and alignment; if at p=none, set a timeline to move forward. – Review spoofing attempts and BEC trends from the past quarter. – People/process: – Run a targeted phishing simulation focused on supplier invoicing, MFA fatigue, and reply-chain hijacking. – Validate your abuse/reporting workflows—how fast do reported phishes get triaged and pulled? – Third-party posture: – Identify top 20 suppliers with email-based workflows; confirm their DMARC posture and security contacts.
60 days – Tech hardening: – Pilot advanced email detection with identity-context integration (impossible travel, OAuth token anomalies). – Implement account anomaly alerts tied to high-risk mail rules (auto-forwarding, external redirects). – OT/IoT visibility: – Conduct an inventory of connected devices in production lines and labs; gap-assess patchability and network placement. – Stand up passive monitoring for critical segments if agents aren’t feasible. – Resilience: – Test restore of critical business systems from clean backups; measure RTO/RPO against objectives.
90 days – Segmentation uplift: – Enforce micro-segmentation around crown-jewel systems; verify least-privilege access paths. – Vendor governance: – Add security SLAs for DMARC enforcement, MFA, and rapid patching in supplier contracts. – Board reporting: – Establish a quarterly risk dashboard with phishing rates, DMARC enforcement status, BEC losses prevented, ransomware tabletop outcomes, and mean time to contain.
Practical email security upgrades you can implement now
- Enforce MFA universally, prioritizing phishing-resistant methods (FIDO2/WebAuthn) for executives and finance.
- Monitor risky mail rules and OAuth grants with automated rollback and user education when anomalies occur.
- Use role-based addresses (ap@, billing@) with tight controls and dedicated training, as they’re common BEC targets.
- Tag external emails clearly; consider warnings on first-contact or lookalike domains.
- Operationalize user-generated intelligence: make the “report phishing” button a first-class sensor and reward prompt reporting.
For healthcare and regulated manufacturers: sector-specific tips
- Map device lifecycle security. Include supplier firmware assurance, SBOMs (software bills of materials), and patch channels in procurement criteria.
- Isolate test/validation equipment. Even non-networked devices often have update pathways—treat them as potential ingress points.
- Build a “safe mode” playbook. Define minimally viable operations during cyber incidents, including manual overrides and clinical safety safeguards.
- Align with frameworks tuned for your world:
- NIST SP 800-53 and 800-82 for OT/ICS
- HICP for healthcare
- FDA premarket cybersecurity guidance for connected devices
External resources: – NIST 800-82: Guide to Industrial Control Systems (ICS) Security – HICP: Health Industry Cybersecurity Practices
Metrics that matter (and the story they tell)
- Phishing resilience score: combination of click rate, report rate, and time-to-report. Narrates human-layer improvement.
- DMARC enforcement coverage: percentage of domains at p=reject with aligned SPF/DKIM. Narrates brand protection maturity.
- BEC containment time: time from first user report to message quarantine and account reset if compromised. Narrates operational readiness.
- Lateral movement dwell time in segmentation tests: narrates blast-radius control.
- Backup restore confidence: percentage of critical systems that meet RTO/RPO in live restore drills. Narrates resilience.
Communicating this to leadership
- The punchline: We’re turning email from our biggest liability into a measured, continually improving control layer by combining authentication, detection, and behavior change—while constraining ransomware blast radius through segmentation and tested recovery.
- The budget lever: Investments that reduce phish success by even a few percentage points yield outsized returns by preventing costly BEC fraud and incident response spend.
- The risk lever: Segmenting critical operations and validating recovery trims worst-case scenarios from weeks to days—material for any enterprise with tight delivery windows.
Further reading and sources
- Osterman Research roundup (May 5, 2026): Daily cybersecurity news
- Sublime Security: Email security platform and resources
- KnowBe4: Security awareness training
- EasyDMARC: DMARC management and enforcement
- Donoma: Company site
- Stryker: Company site
Frequently asked questions
Q: What is DMARC and why should we move to p=reject? A: DMARC tells receiving mail servers how to handle messages that fail SPF/DKIM checks for your domain. Enforcing p=reject prevents direct-domain spoofing from ever reaching inboxes. It’s the single most effective brand-protection step you can take in email, provided you’ve aligned all legitimate senders first.
Q: Will DMARC stop all phishing? A: No. DMARC blocks spoofing of your exact domain, not lookalikes or compromised suppliers. That’s why you still need user training, anomaly detection, and identity-integrated controls.
Q: How do channel partner programs improve security outcomes? A: Strong partners bring standardized playbooks, cross-client threat visibility, 24/7 coverage, and integration muscle across your stack. That often means faster time-to-value and measurable reductions in successful attacks compared to standalone deployments.
Q: What happened in the Stryker incident? A: According to Donoma’s analysis summarized by Osterman Research, Stryker experienced a ransomware event involving exploited vulnerabilities, operational disruption, and concerns about data exposure tied to healthcare IoT and supply chains. Details may evolve, but it underscores the operational stakes of cyber incidents in regulated manufacturing.
Q: We’re small—do we really need advanced email security? A: Yes. Smaller organizations are heavily targeted with commodity phishing and BEC. Channel-delivered solutions make enterprise-grade detection affordable, and DMARC enforcement is table stakes regardless of size.
Q: What’s the quickest win to reduce phishing risk? A: Enforce DMARC (or move decisively toward p=reject), mandate phishing-resistant MFA for high-risk roles, and stand up a rapid triage process for reported phishes. These steps can materially cut risk within weeks.
Q: How do we protect healthcare IoT and OT systems that can’t run agents? A: Use passive network monitoring, strict segmentation, allowlists for communications, and maintenance windows for controlled patching. Pair with jump hosts and MFA for administrator access and maintain detailed asset inventories.
Q: How should we measure success and report to the board? A: Track phishing resilience, DMARC enforcement coverage, BEC containment time, segmentation test results, and backup restore performance. Tie these metrics to incident trends and business continuity posture.
The takeaway
Email is still the adversary’s favorite on-ramp, and ransomware is still the most visible way they cash out. The May 5 news—Sublime’s channel push, a KnowBe4–EasyDMARC tie-up, and the Stryker ransomware analysis—reinforces a simple playbook: authenticate your domains, detect and disrupt malicious messages quickly, condition your people continuously, and design your environment so inevitable compromises don’t become operational crises. Do the basics well, connect the dots between tech and training, and you’ll shrink both the odds and the impact of the next attack.
Discover more at InnoVirtuoso.com
I would love some feedback on my writing so if you have any, please don’t hesitate to leave a comment around here or in any platforms that is convenient for you.
For more on tech and other topics, explore InnoVirtuoso.com anytime. Subscribe to my newsletter and join our growing community—we’ll create something magical together. I promise, it’ll never be boring!
Stay updated with the latest news—subscribe to our newsletter today!
Thank you all—wishing you an amazing day ahead!
Read more related Articles at InnoVirtuoso
- How to Completely Turn Off Google AI on Your Android Phone
- The Best AI Jokes of the Month: February Edition
- Introducing SpoofDPI: Bypassing Deep Packet Inspection
- Getting Started with shadps4: Your Guide to the PlayStation 4 Emulator
- Sophos Pricing in 2025: A Guide to Intercept X Endpoint Protection
- The Essential Requirements for Augmented Reality: A Comprehensive Guide
- Harvard: A Legacy of Achievements and a Path Towards the Future
- Unlocking the Secrets of Prompt Engineering: 5 Must-Read Books That Will Revolutionize You