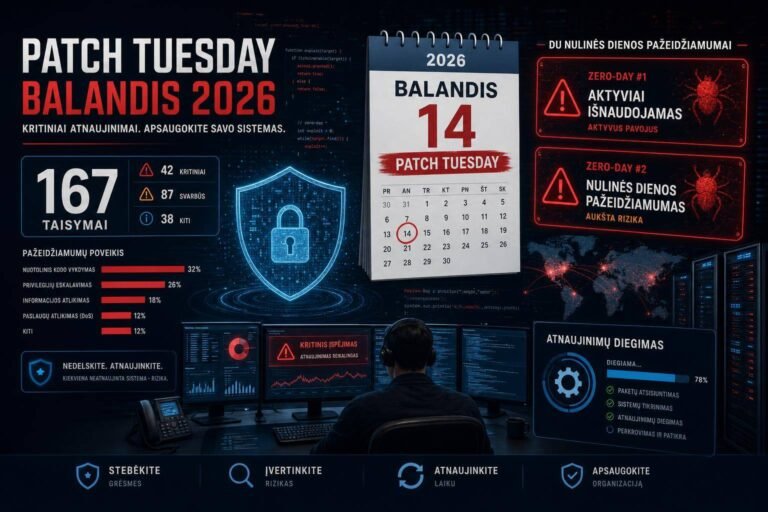
Microsoft’s April 2026 Patch Super Cycle: SharePoint Zero‑Day, IKE RCE, and Defender EoP — What to Patch First
If Microsoft’s April Patch Tuesday felt bigger than usual, that’s because it was. With roughly 169 vulnerabilities fixed—and two zero-days in the wild—this is officially the company’s second‑largest patch release ever. Even more telling: AI‑accelerated discovery is changing where the risk lives, with more privilege‑escalation issues to chain and fewer standalone “click‑and‑own” RCEs.
So what’s urgent, what can wait, and how do you defend while you patch? Let’s break down the zero‑days, the criticals that matter, and a pragmatic, 72‑hour action plan your team can execute right now.
For a concise overview of the original report, see Cyber News Centre’s coverage: 21st April 2026 Cyber Update: Microsoft’s Zero Day – Record Patch Super Cycle in Review.
Why This Patch Tuesday Is Different
- Scale and urgency: Approximately 169 vulnerabilities fixed, making this the second‑largest Microsoft patch release on record.
- Two zero-days to prioritize:
- CVE‑2026‑32201 (SharePoint Server, spoofing; actively exploited).
- CVE‑2026‑33825 (Microsoft Defender, privilege escalation; publicly disclosed).
- One critical, externally reachable RCE:
- CVE‑2026‑33824 (Windows Internet Key Exchange [IKE] Service Extensions), CVSS 9.8, unauthenticated RCE on IKEv2‑enabled VPN endpoints.
- AI-driven discovery pressure: More elevation‑of‑privilege (EoP) bugs are surfacing, enabling attack chains that turn low‑severity footholds into domain‑level compromise. Fewer standalone RCEs doesn’t equal less risk—it means more chaining, faster.
What it means for defenders: Assume compromised endpoints and focus on breaking the chain—patch the exploitable edges, shrink blast radius with segmentation, and double down on detection for identity abuse and lateral movement.
Zero‑Day #1: SharePoint Server Spoofing (CVE‑2026‑32201)
Microsoft has confirmed active exploitation of a spoofing vulnerability in SharePoint Server stemming from improper input validation. Severity is mid‑range (CVSS 6.5), but don’t be lulled—business impact is high because it’s an identity spoofing bug on a collaboration platform often exposed to the internet.
- What attackers can do: Spoof identities via crafted network requests, view protected data, and alter site content. That means content tampering, data exposure, and pivot opportunities into adjacent systems.
- Threat intelligence: Coordinated reconnaissance against internet‑facing SharePoint instances was observed pre‑patch. CISA added this CVE to the Known Exploited Vulnerabilities (KEV) Catalog with a federal remediation deadline of April 28.
- Why it matters: SharePoint is a high‑value target—files, wikis, pages, and internal links are a goldmine for post‑exploitation ops. Spoofed identities can bypass business workflows and trust gateways.
Reference: – CISA KEV Catalog: https://www.cisa.gov/known-exploited-vulnerabilities-catalog – Microsoft Update Guide (track advisories and KBs): https://msrc.microsoft.com/update-guide
How the Attack Works (High Level)
Improper validation allows crafted requests to be processed as if they’re associated with a different identity. In practice, an attacker can:
- Masquerade as a legitimate user to access protected lists, libraries, or pages.
- Modify or inject content (e.g., adding malicious links, tampered documents).
- Seed phishing or internal lateral movement by abusing SharePoint’s trust context.
No single signature catches this—behavioral anomalies are your best friend.
What to Do Right Now
- Patch priority: Highest (internet‑facing and on‑prem SharePoint Server). This is a SharePoint Server issue; SharePoint Online is managed by Microsoft and typically patched by the service.
- Reduce exposure: If you must run SharePoint externally:
- Require MFA/conditional access and limit access via application proxy/VPN.
- Restrict administrative endpoints from public networks.
- Monitor and hunt:
- Look for unusual spikes in failed auth followed by successful access to sensitive sites.
- Review IIS logs for abnormal user‑agents, geolocations, or bursts to “/_api/” and “/_layouts/” endpoints.
- Check for unexpected permission changes, page edits by atypical accounts, or altered list/library content.
- Validate integrity:
- Sample critical pages and libraries for tampering.
- Compare recent backups/snapshots for unapproved content changes.
Useful Microsoft docs: – Updating SharePoint Server: https://learn.microsoft.com/sharepoint/upgrade-and-update/update-sharepoint-server
Critical RCE: Windows IKE Service Extensions (CVE‑2026‑33824, CVSS 9.8)
This is the “front door” risk of the month. The Windows IKE Service Extensions vulnerability allows unauthenticated remote code execution via crafted packets on IKEv2‑enabled VPNs.
- Impact: Pre‑auth RCE on VPN endpoints is a worst‑case perimeter exposure—one missed box equals potential domain foothold.
- Scope: Any Windows host exposing IKEv2 (commonly using UDP 500/4500). That includes edge VPN servers, NVA appliances running Windows, and potentially internal servers if IKE is enabled.
- Mitigation note: Blocking UDP 500/4500 at the perimeter helps—but it does nothing for internal threats or misconfigured segments. Patch remains mandatory.
References: – IKEv2 protocol (RFC7296): https://datatracker.ietf.org/doc/html/rfc7296 – NAT‑Traversal for IPsec (UDP 4500): https://datatracker.ietf.org/doc/html/rfc3947
IKE Exposure Reality Check
- Inventory: Enumerate all VPN endpoints and listen ports (UDP/500, UDP/4500). Don’t forget DR sites and lab environments.
- External surface: Validate exposure with controlled external scanning. If you find unexpected IKE responders on the edge, remove or block them immediately.
- Internal lateral movement: Assume an internal adversary could reach IKEv2 listeners if your segmentation is flat. Patch internal as well as edge‑facing systems.
Immediate Actions
- Patch priority: Highest (tie with SharePoint if externally exposed; otherwise, IKE first).
- Network controls:
- Block/limit UDP 500 and 4500 to only the intended peers.
- Geo/IP restrict where practical.
- Enforce strict ACLs between segments—don’t let workstations reach VPN servers unnecessarily.
- Monitoring:
- Baseline normal IKE traffic; alert on spikes, malformed negotiation attempts, or repeated IKE_SA_INIT failures from unusual IPs.
- Inspect for sudden service crashes/restarts on VPN hosts that could indicate exploitation attempts.
Zero‑Day #2: Microsoft Defender Privilege Escalation (CVE‑2026‑33825)
The second zero‑day is a publicly disclosed local privilege escalation (LPE) in Microsoft Defender. By itself, it won’t get an attacker into your environment—but it dramatically lowers the effort to go from “low‑priv user” to SYSTEM once they’re in.
- Why it matters: EoP bugs are the glue in modern attack chains. Phish a user, drop a payload, escalate via Defender LPE, disable controls, then move laterally.
- Practical risk: Expect this to be rapidly integrated into commodity toolchains and red‑team frameworks.
Actions: – Patch priority: High (immediately after IKE/SharePoint on exposed systems). – Hardening: – Ensure Defender tamper protection is on for servers and clients. – Validate EDR policies preventing Defender manipulation by non‑admin contexts. – Monitoring: – Hunt for suspicious changes to Defender services, exclusions, or policy stores. – Alert on attempts to disable real‑time protection or stop security services. – Update hygiene: – Confirm Defender engine, platform, and intelligence updates are current and on automatic cadence.
References: – Managing Microsoft Defender updates: https://learn.microsoft.com/microsoft-365/security/defender-endpoint/manage-updates-microsoft-defender-antivirus
AI Is Reshaping Vulnerability Patterns
The story behind this patch wave is as important as the CVEs themselves:
- More EoP, fewer standalone RCEs: AI tooling is better at systematically fuzzing and exploring code paths that reveal logic issues and privilege boundary mistakes.
- Chaining is the norm: Adversaries mix initial access (phish, misconfig, weak creds) with EoP to disable controls, dump creds, and pivot.
- Faster time‑to‑weaponization: Publicly disclosed bugs become exploit scripts quickly; zero‑days see broader probing sooner.
Defensive implications: – Harden identity and privilege boundaries—don’t rely on a single control. – Assume a foothold and prioritize blast‑radius reduction (network segmentation, tiering, JIT/JEA, LAPS). – Invest in behavioral detection of identity abuse and lateral movement rather than relying only on signature‑driven detections.
Reference: – MITRE ATT&CK (Privilege Escalation): https://attack.mitre.org/tactics/TA0004/
A 72‑Hour Patch and Protection Plan
Day 0–1 (Triage and Immediate Risk Reduction) – Freeze non‑essential changes; open a change window for emergency patching. – Prioritize assets: 1) Internet‑facing SharePoint Server. 2) All IKEv2‑enabled VPN endpoints (edge first, then internal). 3) High‑value servers and jump hosts with Microsoft Defender. 4) Remaining Windows servers and critical workstations. – Exposure controls: – Temporarily restrict internet access to SharePoint admin endpoints where possible. – Geo/IP restrict VPN sources and enforce MFA for all remote access. – Block unnecessary east‑west UDP 500/4500. – Telemetry: – Increase log retention and EDR sensitivity during the patch window. – Baseline and watch IKE traffic and SharePoint HTTP patterns for anomalies.
Day 1–2 (Patch Deployment and Validation) – Patch sequencing: – Apply Microsoft updates to SharePoint and VPN hosts first. – Validate service health after each patch (SharePoint site availability, VPN tunnel stability). – Defender updates: – Confirm latest Defender platform/engine/intelligence installed. – Validate tamper protection and policy integrity on key systems. – Verification: – Sample SharePoint sites for unauthorized changes. – Run controlled VPN connection tests from allowed geographies. – Review logs for any post‑patch exploitation attempts.
Day 2–3 (Hunting and Hardening) – Hunt for indicators: – SharePoint: suspicious page edits, permission changes, elevated activity from atypical users. – VPN: bursts of failed IKE negotiations, scans against UDP 500/4500, odd source ASN or region. – Workstations/servers: attempts to modify Defender, spawn processes as SYSTEM from non‑admin accounts. – Hardening: – Ensure segmentation rules prevent workstations from reaching VPN servers and SharePoint admin paths. – Enforce least privilege and Privileged Access Workstations (PAWs) for admins. – Review conditional access/MFA enforcement for all external access. – Exceptions: – Document any systems that cannot be patched; apply compensating controls (ACLs, isolate to separate VLANs, increase monitoring) with owner sign‑off and review cadence.
Detection and Hardening Checklist
SharePoint Server – Patch to latest supported build; confirm success across all farm nodes. – Review IIS logs for: – Spike in 401/403 followed by 200s on sensitive endpoints. – Unusual user‑agents or IPs accessing “/_api/” and “/_layouts/”. – Audit: – Recent site/page/library permission changes. – Unapproved page edits or web part modifications.
Windows IKEv2/VPN – Patch all IKEv2‑enabled servers and clients participating in VPN roles. – Firewall: – Edge: restrict UDP 500/4500 to known peers. – Internal: block unnecessary UDP 500/4500 east‑west. – Monitor: – IKE_SA_INIT spikes, malformed handshakes, unusual geo sources. – VPN service instability or crashes around patch time.
Microsoft Defender – Confirm latest platform/engine/intelligence versions. – Enforce tamper protection and EDR policy integrity. – Alert on: – Changes to Defender exclusions or real‑time protection state. – Processes acquiring SYSTEM from low‑priv contexts unexpectedly.
Identity and Network – Enforce MFA and conditional access for all external entry points. – Segmentation: isolate management planes and admin interfaces. – PAM practices: JIT/JEA for admin rights, LAPS for local admin password rotation.
Threat Hunting Ideas (No Special Tools Needed)
- Unusual SharePoint behavior:
- Users with no prior history editing high‑sensitivity sites suddenly making changes.
- Large volumes of list/library reads from unfamiliar IPs.
- VPN anomalies:
- New or rare ASNs attempting connections.
- Repeated initiation attempts with no successful tunnel establishment.
- EoP patterns:
- Non‑admin accounts spawning processes as SYSTEM.
- Sudden Defender policy changes followed by credential dumping or LSASS access attempts.
If you have EDR/XDR, create temporary high‑sensitivity alerts for these behaviors during the patch window.
Communicating Risk to Stakeholders
- Executive summary: “Two zero‑days (SharePoint spoofing and Defender EoP) and one critical pre‑auth VPN RCE require emergency patching. We’re prioritizing internet‑facing systems first and implementing compensating network controls to reduce exposure while we patch.”
- Timeline: Present a 72‑hour plan with checkpoints and rollback procedures.
- Metrics: Number of systems exposed, patched, isolated, and under enhanced monitoring.
- Residual risk: Identify any exceptions and compensating controls with clear owners.
Common Pitfalls to Avoid
- Treating CVSS as gospel: A 6.5 spoofing bug in SharePoint is high impact in context. Patch by business risk, not just score.
- Perimeter‑only thinking for IKE: Blocking UDP 500/4500 at the edge doesn’t address internal exposure. Patch anyway.
- Delaying Defender updates: EoP flaws get operationalized fast. Keep Defender current and tamper‑protected.
- Ignoring content integrity: If SharePoint was abused for spoofing, audit for silent content tampering and permission drift.
Useful Resources
- Cyber News Centre coverage: 21st April 2026 Cyber Update
- Microsoft Security Update Guide (official advisories/KBs): https://msrc.microsoft.com/update-guide
- CISA KEV Catalog: https://www.cisa.gov/known-exploited-vulnerabilities-catalog
- Microsoft Defender update guidance: https://learn.microsoft.com/microsoft-365/security/defender-endpoint/manage-updates-microsoft-defender-antivirus
- IKEv2 standard (RFC7296): https://datatracker.ietf.org/doc/html/rfc7296
- NCSC on network segmentation (10 Steps): https://www.ncsc.gov.uk/collection/10-steps-to-cyber-security/network-security
- MITRE ATT&CK Privilege Escalation: https://attack.mitre.org/tactics/TA0004/
FAQs
Q: Is SharePoint Online affected by CVE‑2026‑32201?
A: The vulnerability targets SharePoint Server (on‑prem). SharePoint Online is managed by Microsoft and is typically remediated by the service provider. If you run hybrid, ensure your on‑prem farm is fully patched.
Q: We don’t think we use IKEv2—are we safe from CVE‑2026‑33824?
A: Validate, don’t assume. Inventory VPN roles and scan for UDP 500/4500 listeners. Some templates or legacy roles can enable IKEv2 implicitly. Patch regardless on systems that have IKEv2 enabled.
Q: Is blocking UDP 500/4500 at the perimeter enough?
A: No. It reduces external exposure but doesn’t eliminate internal risk or misconfigurations. Patch is mandatory, and you should also restrict east‑west traffic where feasible.
Q: How fast do we need to patch SharePoint?
A: Treat it as an emergency. Active exploitation is reported, and CISA has set an April 28 deadline for federal agencies. Internet‑facing instances should be remediated immediately.
Q: What should we watch for to detect SharePoint spoofing abuse?
A: Look for anomalous access patterns to “/_api/” and “/_layouts/”, unexpected page edits or permission changes, and successful access to sensitive resources following a burst of failed auth attempts. Also, review for content tampering.
Q: How do I confirm Microsoft Defender is up to date against CVE‑2026‑33825?
A: Ensure your Defender platform, engine, and intelligence are current and set to auto‑update. Validate tamper protection is on. See Microsoft’s guidance: manage updates.
Q: Do we need reboots after patching?
A: Many Windows patches, especially kernel or networking stack updates, require reboots. Schedule maintenance windows and verify service health post‑reboot (e.g., VPN tunnels, SharePoint farm availability).
Q: We can’t patch a critical server this week. What compensating controls help?
A: Isolate it to a protected VLAN, restrict inbound UDP 500/4500 to known peers, enforce MFA/conditional access for any interactive access, increase logging/EDR sensitivity, and monitor aggressively. Document the exception with a remediation date.
Q: Are macOS/Linux endpoints affected by these CVEs?
A: These CVEs target Microsoft products (SharePoint Server, Windows IKE, Microsoft Defender). However, multi‑platform environments are still at risk from identity abuse and lateral movement—keep your cross‑platform EDR and identity controls tight.
Q: What’s the single most important action to take today?
A: Patch internet‑facing SharePoint and IKEv2 VPN endpoints immediately, then validate Defender is fully updated and tamper‑protected. In parallel, restrict exposure (UDP 500/4500, admin paths) and enable heightened monitoring.
The Bottom Line
This “super cycle” is a clear signal: the vulnerability landscape is accelerating, and chaining is the new normal. Two zero‑days and a critical pre‑auth VPN RCE leave little room for delay. Patch SharePoint Server and IKEv2 endpoints now, update Defender across the fleet, and assume a foothold as you harden identity, segmentation, and monitoring. Organizations that move quickly in the next 72 hours will meaningfully reduce the blast radius—and stay a step ahead of both nation‑state and criminal campaigns.
Discover more at InnoVirtuoso.com
I would love some feedback on my writing so if you have any, please don’t hesitate to leave a comment around here or in any platforms that is convenient for you.
For more on tech and other topics, explore InnoVirtuoso.com anytime. Subscribe to my newsletter and join our growing community—we’ll create something magical together. I promise, it’ll never be boring!
Stay updated with the latest news—subscribe to our newsletter today!
Thank you all—wishing you an amazing day ahead!
Read more related Articles at InnoVirtuoso
- How to Completely Turn Off Google AI on Your Android Phone
- The Best AI Jokes of the Month: February Edition
- Introducing SpoofDPI: Bypassing Deep Packet Inspection
- Getting Started with shadps4: Your Guide to the PlayStation 4 Emulator
- Sophos Pricing in 2025: A Guide to Intercept X Endpoint Protection
- The Essential Requirements for Augmented Reality: A Comprehensive Guide
- Harvard: A Legacy of Achievements and a Path Towards the Future
- Unlocking the Secrets of Prompt Engineering: 5 Must-Read Books That Will Revolutionize You