Here you can find all and the most recent posts of InnoVirtuoso.com, if anything you can browse around the categories you find interesting.
-
AI Update (May 2026): OpenAI Ads in ChatGPT, GPT‑5.5 Instant, Agentic Assistants, Apple Model Choices, and U.S. Security Stress Tests
Commercialization, autonomy, and oversight are colliding in generative AI. The past week’s AI update saw OpenAI turn ChatGPT into an ad platform, shipped a faster default model…
-
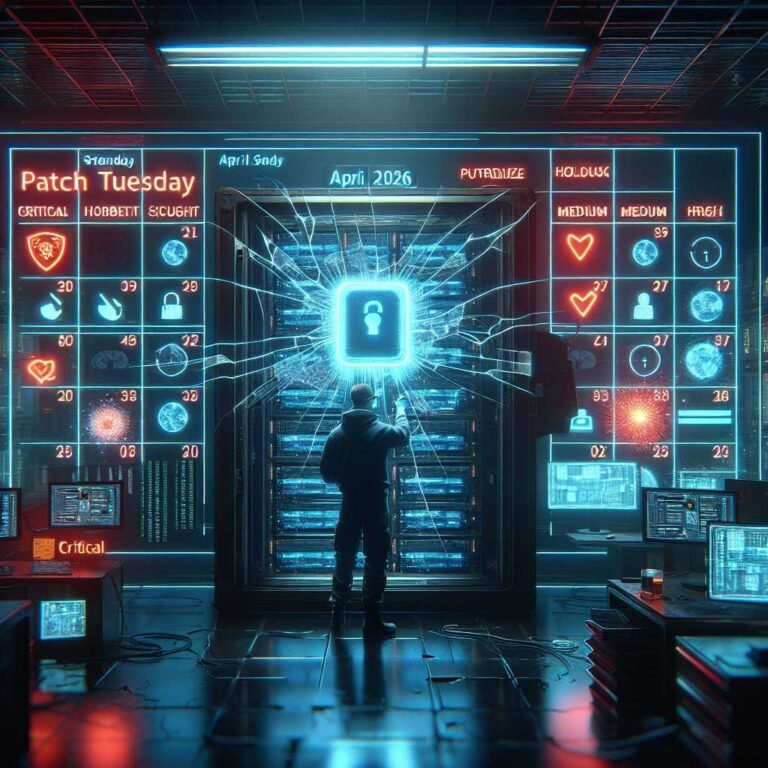
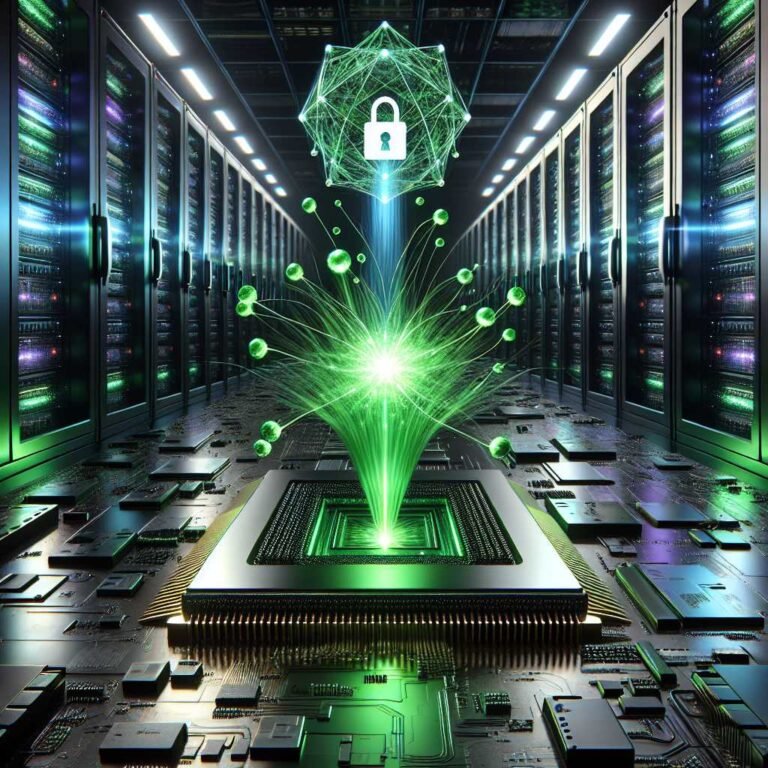
Patch Tuesday May 2026: CVE Analysis, Pre‑Auth RCEs, and the Rise of AI‑Discovered Bugs
Microsoft’s Patch Tuesday for May 2026 is a wake‑up call for enterprise defenders. Beyond the usual cadence of critical fixes, this month highlights how fragile core network…
-
Patch Tuesday May 2026: Prioritize CVE-2026-41089 in Windows Netlogon and Other Critical Microsoft Fixes
May’s Patch Tuesday lands with a stark message for enterprise defenders: domain controllers should be at the front of your queue. Microsoft’s May 2026 security updates tackle…
-
May 2026 Patch Tuesday: 30 Critical Microsoft Vulnerabilities, DNS Client RCE and Azure DevOps Data Exposure Top the List
Microsoft’s May 2026 Patch Tuesday is one of the year’s most consequential security updates: 130 CVEs fixed, 30 rated Critical, and several pre‑auth, internet‑exposed flaws with remote…
-
OpenAI’s GPT‑5.5 Instant: The New Default ChatGPT Model, Safety Tested and Enterprise‑Ready
OpenAI has introduced GPT‑5.5 Instant as the new default behind ChatGPT and the primary API endpoints—a change that matters for anyone shipping AI into production or protecting…
-
How Adversaries Leverage AI for Vulnerability Exploitation, Augmented Operations, and Initial Access
State-backed operators and profit-driven cybercriminals aren’t waiting for the future of AI-enabled attacks—they’re shipping them now. Google Cloud’s Threat Intelligence Group just published research showing how adversaries…
-
AI and Crypto Super PACs vs. Voters: Why the 2026 Midterms Face a Trust Gap—and How Candidates Should Respond
The money is loud, but the electorate is skeptical. An April 2026 poll highlighted by Politico signals a widening gap between the agendas of deep-pocketed AI and…
-
AI | Regulation
EU Commission Weighs Pause on AI Act Application: What It Means for High‑Risk AI Compliance, Timelines, and Strategy
Europe’s flagship AI regulation may be getting a strategic breather. Reports indicate the European Commission is considering a pause on parts of the EU AI Act’s entry…
-
EU AI Act at a Crossroads: Why Europe May Delay and Dilute AI Regulations—and How to Future‑Proof Your Compliance
Europe’s landmark AI regulation is about to leave the drafting table and enter the real world. Yet just as key obligations near their start date, lawmakers are…
-
AI Regulations Are Already Lagging: How IT Leaders Can Build Future‑Proof Governance Before Enforcement Hits
AI is moving faster than the rulebooks written to contain it. Models now generate code, orchestrate tools, and act in semi‑autonomous “agentic” workflows. Meanwhile, compliance teams are…
-
May 2026 Cybersecurity Roundup for Startups: AI Threats, People Risk, and Defensive Automation
Founders and small teams just got a reality check: cybersecurity is now a people risk issue as much as a technical one. This May, risk analysts and…
-
April 2026 Cyber Attacks: Major Data Breaches, Ransomware Incidents, and Zero‑Day Exploits—and How to Respond
April 2026 wasn’t just another noisy month in cybersecurity headlines—it marked a measurable jump in successful intrusions, exploited vulnerabilities, and ransomware operations across sectors worldwide. Reports highlighted…
-
2026 and the Rise of AI-Based Cyberattacks: Threat Models, Real Risks, and a Zero-Trust Playbook for Resilience
AI has crossed a threshold. For attackers, it’s no longer just a research toy or a niche capability—it’s a force multiplier. In 2025, a major analyst survey…
-
AI | Regulation
EU AI Act August 2026 Deadline: A Practical Compliance Roadmap for U.S. Companies
U.S. software and AI providers that operate in Europe—or whose systems impact EU residents—are on the clock. The EU Artificial Intelligence Act’s high-risk obligations are slated to…
-
AI Update: May 8, 2026 — Autonomous Agents, ChatGPT Ads, and Apple’s Third‑Party AI Bet
A pivotal AI update this week signals the industry’s turn from chat to action. Three forces are converging: consumer-facing monetization inside assistants, platform openness to multiple model…
-
RSAC 2026 Takeaways: AI in Cybersecurity Is Moving From Co‑Pilots to Autonomous SOC Agents
AI in cybersecurity just hit a new speed class. What had been a wave of “co‑pilots” and assistant features is now converging into integrated, agentic systems that…
-
AI Innovations and Cybersecurity Threats on May 3, 2026: Uber’s Fleet-as-Sensors, Embodied AI Moves, and the Governance Fight
Artificial intelligence didn’t just make headlines on May 3, 2026—it collided with the real world. Uber signaled a bold plan to turn millions of driver journeys into…
-
Cybersecurity and AI Predictions for 2026: Six Trends Redefining Attacks, Defenses, and Risk
AI isn’t just augmenting cybersecurity—it’s changing its physics. The same models that help us write code, triage alerts, and hunt threats are now capable of generating working…
-
Inside CVE-2026-26133: M365 Copilot AI Command Injection Information Disclosure Vulnerability and How to Defend
Microsoft 365 Copilot turned office productivity into a conversational interface. It also expanded the enterprise attack surface in ways many security teams are still learning to model….
-
AI Regulation in 2026: A Practical Guide to the EU’s Risk-Based Rules, US State Laws, and What Builders Must Do Now
The rules of AI have finally arrived. 2026 is not a prelude—it’s enforcement. If you build, buy, or deploy AI systems at any scale, the legal and…
-
AI | Regulation
EU Rejects ‘Stop-the-Clock’: What the 2026 EU AI Act Compliance Deadlines Mean for Builders, CIOs, and Legal Teams
Europe just told the global AI industry there’s no more time to negotiate with the calendar. With the European Commission rejecting calls for a two-year “Stop-the-Clock” moratorium,…
-
May 3, 2026 Briefing: AI and Cybersecurity Collide—Breakthroughs, Breaches, and What Leaders Must Do Next
The first week of May delivered a stark snapshot of where AI and cybersecurity stand in 2026: astonishing technical progress, heightened misuse, and escalating real‑world stakes. On…
-
AI Cybersecurity in 2026: Trends, Threats, and a Playbook for Defenders
AI is now embedded in both sides of the cyber arms race. Security teams are adopting generative models to spot anomalies, triage alerts, and accelerate response. Attackers…
-
AI Legislative Update (May 8, 2026): State Bills Target Chatbot Safety, AI Disclosures, Frontier Developer Duties, and Content Labels
Statehouses are putting real teeth into AI governance. While federal activity moves in parallel, this week’s state-level AI legislative update features a clear theme: lawmakers want practical…
-
When Empathy Backfires: Oxford Study Finds ‘Kinder’ AI Language Models Are 60% More Likely to Get Answers Wrong
Artificial intelligence teams have spent the last few years making large language models sound more human—friendlier, more supportive, more emotionally attuned. But new research from Oxford University…
-
CISA Orders Rapid Patching of Windows Zero‑Day CVE‑2026‑32202 as Pass‑the‑Hash Risk Escalates
A new Windows zero‑day, CVE‑2026‑32202, has moved from a technical curiosity to an urgent enterprise priority. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the flaw…
-
AI | Regulation
2026 AI Laws Update: Federal Preemption, New Agency Actions, and a Practical Compliance Playbook
The ground under U.S. AI governance is shifting fast. In December 2025, President Trump signed an executive order that aims to consolidate AI oversight at the federal…
-
Claude Mythos Revealed: Autonomous Hacking Capabilities and the Federal AI Safety Legislation They Triggered
On May 4, 2026, reports that Anthropic’s restricted frontier model—Claude Mythos—can autonomously identify and exploit zero-day vulnerabilities jolted AI and security communities into a new reality. Mythos…
-
AI Security Flashpoint: Anthropic’s ‘Claude Mythos’ Zero‑Day Revelations, UK DSIT Warning, and NVIDIA’s Quantum‑AI Push — May 2026 AI Round‑Up
AI and cybersecurity just collided in a way few expected to see this soon. Reports around Anthropic’s Claude Mythos Preview—a frontier model allegedly capable of autonomously finding…
-
Big Tech’s $600B AI Spending Race in 2026: Chips, Data Centers, Power—and the Path to Returns
Investors and operators are staring at the same question from opposite sides of the glass: when will massive AI spending turn into durable, high-margin revenue? With Alphabet,…
-
Google Expands Pentagon Access to Its AI: Inside the Classified Deal, the Tech Stack, and What It Means After Anthropic’s Refusal
Google’s classified agreement to expand the Pentagon’s access to its AI marks a decisive moment in the fusion of commercial AI with U.S. national security. With Anthropic…
-
AI News Briefing, April 2026: Microsoft–OpenAI FedRAMP Breakthrough, DeepSeek Pricing Shock, Google Safety Letter, and More
The week delivered a rare convergence of AI news that matters in the trenches: a compliance unlock for government AI, a price jolt that resets unit economics,…
-
AI News Briefs for April 2026: GPT‑5.5, Meta’s Muse Spark, and Agentic Automation for Data Science
April 2026 didn’t just add another month of AI product updates—it brought a new tempo to how reasoning, tool use, and automation are converging in real-world systems….
-
AI News Briefing: Ineffable Intelligence Raises $1.1B, OpenAI–Microsoft Go Multi‑Cloud, Meta Bets on Space Solar, and Agentic MLOps Hits AWS
The past week’s AI news wasn’t just a series of funding headlines—it was a coherent signal about where AI is actually going: beyond data moats, across clouds,…
-
OpenAI Achieves FedRAMP Moderate on Azure Government: Implications for Secure AI Adoption Across U.S. Agencies
OpenAI’s April 28, 2026 announcement that its enterprise offerings—including GPT-5.5 and custom GPTs—are now available at FedRAMP Moderate via Microsoft Azure Government is more than a compliance…
-
AI Costs vs. Human Labor: Why a Nvidia Executive Says the Cost of AI Tools Is “Far Beyond” Employees—and How to Fix It
The math behind generative AI in 2026 is unsettling: for many use cases, the fully loaded cost of AI tools still exceeds the cost of people. A…
-
Startup News Today April 28, 2026: Europe’s $1.1B AI Seed Milestone, China Blocks Meta–Manus Deal, and OpenAI’s Enterprise Agents Move Ahead
Europe just posted its largest AI seed round on record. China stepped in to halt a high-profile U.S.–China AI deal on security grounds. And OpenAI is leaning…
-
State of AI 2026: April Update on Power Shifts, Frontier Models, and the Energy Constraint
April 2026 compressed a year of AI volatility into four weeks. Frontier model launches clustered into days, global investment blasted past expectations, the UN opened the door…
-
Oral Exams to Combat AI: How Universities Are Restoring Mastery and Integrity in Higher Education
Generative AI has made it easier than ever to produce flawless essays and well-structured problem sets on demand. But many instructors now see a troubling gap: students…
-
AI Today, April 29, 2026: Big Tech’s $130B Quarter, Copilot’s 20M Seats, TPU Bottlenecks, and What Comes Next
The AI story today isn’t about demos—it’s about deployment pressure. Big Tech’s AI spending surge hit $130 billion in Q1, Microsoft crossed 20 million paid Copilot seats…
-
OpenAI and Microsoft End Exclusive Partnership: What It Means for Cloud AI, Anthropic, and Enterprise Model Strategy (April 2026)
The AI power map shifted overnight. On April 29, 2026, OpenAI and Microsoft ended their exclusive software deal, freeing OpenAI to work with other hyperscalers while Microsoft…
-
AI News Intelligence Digest — April 29, 2026: $242B AI VC Surge, Mega-Rounds, and What It Means for Builders and CISOs
Quarter one of 2026 reset the baselines for artificial intelligence investment. Global venture funding reached roughly $300 billion, and AI alone captured an estimated $242 billion—about 80%…
-
Top Tech News Today (April 29, 2026): Musk’s OpenAI Testimony, China Blocks Meta’s AI Deal, and Google’s Pentagon Pact Signal a New AI Power Struggle
A single day’s headlines can reset the arc of a technology era. On April 29, 2026, three developments did just that: Elon Musk’s courtroom testimony alleging OpenAI…
-
Inside OpenAI’s Stargate: How Hyperscale AI Compute Infrastructure Is Being Built for the Intelligence Age
Artificial intelligence is running headlong into the limits of today’s computing footprint. Training frontier models, powering conversational agents at population scale, securing LLM supply chains, and enabling…
-
AI News Roundup (April 17–29, 2026): GPT-5.5, Google’s Agent Platform, EU AI Rules, and the Race to 10 GW
The closing days of April delivered one of the most consequential bursts of AI activity this year. Regulatory gears in the EU slipped just as hyperscale infrastructure…
-
AI Advertising And The Misinformation Risk: UN Warns Of Deepfakes, Hyper‑Personalization, And Election Interference
AI advertising has entered its “agentic” phase. Models that can generate, place, and optimize ad creative across channels—without a human in the loop—are now driving budgets measured…
-
SoftBank Launches Roze AI, a Robotics Company to Build Data Centers 10x Faster
SoftBank just placed a very public bet that the physical bottlenecks of the AI era can be solved by robots. On April 29, 2026, the company announced…
-
AI & Data Science Daily — April 29, 2026: Agentic AI Hits Revenue Scale, Cloud Chips Mature, and the Infrastructure Race Heats Up
Cloud earnings now read like a referendum on AI strategy. In the April 29 AI & Data Science Daily briefing, multiple signals converged: agentic AI is moving…
-
AI News April 29–30, 2026: Agentic AI Hits Production, Cloud Earnings, TPU Advances, and Search Shake‑Ups
Two days just redrew the AI map. In 24 hours, the world’s largest platforms made it clear that the center of gravity in AI has moved from…
-
CISA orders immediate patching of Windows zero-day CVE-2026-32202 after active exploitation
A critical Windows zero-day vulnerability is being exploited in the wild, and the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has ordered federal agencies to patch without…
-
April 2026 Cyber Attacks: Major Data Breaches, Ransomware Campaigns, and Zero‑Days That Should Reshape Your Security Roadmap
April 2026 delivered a hard reset on what “normal” looks like in cyber defense. Supply-chain compromises rode in through developer tooling, nation-states pivoted to identity and DNS…
-
Microsoft Impersonation Phishing Spikes in 2026: How Hackers Are Breaching Microsoft 365—and How to Stop Them
Attackers are leaning hard on brand trust. In late April 2026, security teams saw a surge in hackers impersonating Microsoft to steal credentials and hijack enterprise Microsoft…
-
Daily CyberTech Highlights: CISA KEV Updates, Windows Zero‑Click, ScreenConnect RCE, Medtronic Breach, and Post‑Quantum Ransomware (April 29, 2026)
The April 29 Daily CyberTech Highlights snapshot brings a blunt message: exploit velocity is outpacing most patch cycles. CISA has added two high-pressure entries to the Known…
-
Cybersecurity Daily Briefing: Patch Windows CVE-2026-32202, ScreenConnect, LiteLLM, and cPanel Now as Exploits Accelerate
Threat actors aren’t waiting. Within days of disclosure, attackers began weaponizing fresh flaws in Microsoft Windows (CVE-2026-32202), ConnectWise ScreenConnect, LiteLLM, and cPanel. The result: reliable paths to…
-
Medtronic Breach: Why “No Operational Impact” Still Leaves Healthcare Exposed—and What To Do Next
Medtronic’s April 2026 disclosure that a third party accessed parts of its corporate IT environment landed with a familiar refrain: no disruption to products, therapies, or patient…
-
CISA Adds Microsoft Windows Shell CVE-2026-32202 and ConnectWise ScreenConnect to the KEV Catalog: Patch Deadlines, Active Exploits, and How to Respond
Two more high-risk holes just landed in the crosshairs. On April 29, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a Microsoft Windows Shell vulnerability…
-
Cyber Daily News (April 29, 2026): CISA KEV Adds Windows Shell and ScreenConnect; GitHub RCE CVE-2026-3854; Vect Ransomware Wiper Risk; Handala Targets US Troops
Security teams got a crowded docket this week. In fast succession, CISA added actively exploited Microsoft Windows Shell and ConnectWise ScreenConnect flaws to its Known Exploited Vulnerabilities…
-
CISA Adds Actively Exploited Windows Shell and ConnectWise ScreenConnect Flaws to the KEV Catalog: Patch Deadlines, Threat Details, and a Defense Playbook
Two more actively exploited vulnerabilities just landed in CISA’s Known Exploited Vulnerabilities (KEV) catalog: a Windows Shell bug tracked as CVE-2026-32202 and an undisclosed ConnectWise ScreenConnect flaw….
-
CVE-2026-32202: Zero-Click Windows Shell Flaw Actively Exploited After Incomplete Patch
Microsoft and the U.S. Cybersecurity and Infrastructure Security Agency (CISA) are warning that a new Windows zero-click vulnerability, CVE-2026-32202, is being exploited in the wild. The flaw…
-
Big Tech AI Spending Surges Past $700B in 2026: What It Means for Cloud, Chips, and the Enterprise
The world’s largest tech companies just pressed the accelerator on AI infrastructure. Alphabet, Meta, Microsoft, and Amazon collectively disclosed more than $130 billion in Q1 capital expenditures—largely…
-
Stripe Link Opens to Autonomous AI Agents: Secure Digital Wallet Payments for Software-Driven Commerce
Autonomous AI agents are moving from the sidelines to the checkout line. With Stripe updating its Link digital wallet to be usable by autonomous software, the idea…
-
Meta’s AI Investment Surge and OpenAI’s Legal Challenges: Multi‑Cloud GPT‑5.5 and the New Economics of Enterprise AI
Meta’s AI investment surge and OpenAI’s legal challenges arrive at a moment when the economics, energy, and ethics of frontier models are all in flux. Billions more…
-
AI News Roundup for April 30, 2026: OpenAI’s ‘Goblin’ Data Bug, Anthropic Mythos NSA Tests, 10GW Compute, and Agentic Automation
On April 30, 2026, the AI sector moved fast—and not just on benchmarks. OpenAI explained a strange “goblin” anomaly in its models as a rare data contamination…
-
Salesforce Is Crowdsourcing Its AI Roadmap With Customers: Inside the Push for Practical Enterprise AI
Salesforce is putting its foot on the gas of enterprise AI adoption by doing something deceptively simple: asking customers what to build next. Crowdsourcing an AI roadmap…
-
MediaTek Doubles Its 2026 AI ASIC Ambitions: $2B Revenue Target and a Bid for 10–15% of Custom AI Accelerators
MediaTek is turning up the heat in the AI silicon race. According to multiple reports citing CEO Rick Tsai, the company has doubled its 2026 revenue target…
-
AI Regulation Crackdown and China’s 60% Patent Share: Compliance Impacts and the New AI Arms Race
AI went macro this quarter. Beijing is tightening the screws on algorithm governance while the Digital China Development Report claims China now holds 60% of the world’s…
-
White House Rallies Big Tech Against AI-Driven Cyberattacks: What’s Changing and How to Prepare
The White House has asked some of the world’s most powerful AI and cybersecurity companies to help contain a fast-moving threat: AI-driven cyberattacks. According to a recent…
-
Microsoft Research Backs Georgia Tech’s Push to Build Collaborative AI Systems for Real-World Teams
Human-AI collaboration is moving past autocomplete and chatty copilots. The next frontier is teams of AI agents that coordinate with people in real time—negotiating roles, sharing context,…
-
Inside Big Tech’s $700 Billion AI Infrastructure Spending Surge: Data Centers, GPUs, and the Power Constraint
The world’s largest tech companies are on track to pour roughly $700 billion into AI infrastructure in 2026, with no clear off-ramp. That spending isn’t just about…
-
cPanel Authentication Bypass Zero‑Day (CVE‑2026‑41940): Active Exploitation, Emergency Patches, and How to Respond Now
A critical cPanel authentication bypass zero-day, tracked as CVE‑2026‑41940, is being actively exploited and gives unauthenticated attackers full administrative access to cPanel and WHM servers. With a…
-
CVE-2026-32202: Incomplete Windows SmartScreen Patch Enables Zero-Click Attacks and NTLM Hash Theft
Akamai researchers uncovered that an incomplete Microsoft patch quietly opened a fresh zero-click pathway into Windows networks—and adversaries didn’t need a single user interaction to get in….
-
Email threat landscape Q1 2026: 8.3B phishing attempts and a 146% surge in QR code attacks
Phishing didn’t slow down in early 2026—it evolved. Microsoft Threat Intelligence reports 8.3 billion phishing attempts in Q1 2026, with attackers shifting tactics to outpace filters and…
-
White House Calls on Tech to Counter AI Cyber Threats: What Advanced Models like Anthropic’s ‘Mythos’ Mean for Security Strategy
The White House has asked leading technology and cybersecurity companies to weigh in on how advanced AI systems—including models like Anthropic’s reported “Mythos”—could be weaponized in cyberspace….
-
U.S. Army Enlists Tech Giants to Build AI Cyber Defense for Machine‑Speed Threats
The U.S. Army has tapped leaders from cloud, cybersecurity, and AI to help chart a path for automated defenses as cyberattacks accelerate to machine speed. The move…
-
Active Exploitation of cPanel/WHM Vulnerability (CVE-2026-41940): What Web Hosts and Site Owners Must Do Now
A critical cPanel/WHM vulnerability, tracked as CVE-2026-41940, is under active exploitation — and it directly targets the login flow that tens of millions of websites rely on…
-
Critical cPanel & WHM Zero‑Day (CVE-2026-41940): Authentication Bypass Exploited for Months—and What to Do Now
A critical authentication bypass in cPanel & WHM (CVE-2026-41940, CVSS 9.8) has been exploited as a zero‑day since late February 2026. The flaw grants full control of…
-
Inside the Python Backdoor DEEP#DOOR: How Tunneling Services Enable Stealthy Browser and System Data Theft
A newly observed Python backdoor framework dubbed DEEP#DOOR shows how quietly modern malware can burrow into Windows systems, persist across reboots, and siphon off sensitive browser and…
-
cPanel Zero-Day CVE-2026-41940: Active Exploitation Timeline, Patching Guidance, and Incident Response Playbook
A critical authentication bypass in cPanel (CVE-2026-41940, CVSS 9.8) has been exploited in the wild for weeks, granting attackers full control over hosting servers and the websites…
-
Zero Trust for Operational Technology: What CISA’s New Joint Guide Means for Critical Infrastructure
A wave of high-impact attacks on industrial control systems has pushed operational technology from the plant floor to the boardroom. Now, U.S. federal agencies led by the…
-
Vishing and SSO Abuse: How Cybercrime Groups Orchestrate Rapid SaaS Takeovers—and How to Stop Them
Two things are reshaping enterprise breaches right now: phones and identity. Since late 2025, coordinated cybercrime crews have been running high-speed SaaS intrusions that start with a…
-
Top 5 Cybersecurity News Stories (May 1, 2026): Entra ID Agent Takeover Risk, REvil/GandCrab Breakthrough, BlueHammer Malware, nginx-ui RCE, and ScreenConnect CVE-2024-1708
Cybersecurity didn’t take a holiday. The biggest headlines this week concentrate on identity security failures, ransomware pressure, endpoint blind spots, vulnerable admin surfaces, and abused remote access….
-
Life Sciences Cyber Threats: Protecting IP, Clinical Trial Data, and AI Systems Amid Rising Attacks
Life sciences companies are in the crosshairs. As biopharma, medtech, and research organizations digitize discovery and clinical operations, attackers are following the data—intellectual property, clinical trial datasets,…
-
Cybersecurity Report 2026: 70% of U.S. Infrastructure Compromised and QR Code Phishing Surges 146% — What It Means and What to Do Now
A new cybersecurity report, released May 1, 2026, signals a sobering reality: an estimated 70% of U.S. infrastructure has been compromised, while QR code phishing (often called…
-
UK Cyber Security Breaches Survey 2025/2026: 43% of Businesses Hit as Phishing Dominates
The UK’s latest Cyber Security Breaches Survey for 2025/2026 reports a stark headline: 43% of businesses and 28% of charities experienced a cyber incident in the past…
-
CISA and NSA Guidance for Secure Adoption of Agentic AI: Risks, Controls, and a Practical Playbook
Autonomous agents are moving from research demos into real workflows—triaging support queues, moving money between accounts, updating records in ERP systems, even touching elements of critical infrastructure….
-
April 2026 Cyber Attacks Surge: Ransomware, Zero‑Days, and What Security Teams Must Do Now
April 2026 did not just notch another month of cyber attacks; it marked a step-change in how fast adversaries weaponize vulnerabilities and pivot across sectors. Government bodies,…
-
China‑Linked Hackers Exploit Microsoft Exchange Vulnerabilities in Multi‑Year Espionage Targeting Asia and a NATO State
A newly detailed, long-running espionage operation attributed by researchers to China-aligned actors has quietly burrowed into government and defense networks across South, East, and Southeast Asia—and reached…
-
KRYBIT Ransomware Campaign: Double‑Extortion Tactics, Rapid Timeline, and Defense Playbook for Global Enterprises
A fast-moving ransomware operation attributed to the KRYBIT group is targeting organizations across Europe, Asia, and the Americas, combining data theft with encryption to maximize pressure on…
-
Handala Hack’s WhatsApp Threats to US Troops: Cyber-Enabled PSYOPS, OPSEC Gaps, and How to Respond
US service members deployed in the Middle East have reportedly received threatening WhatsApp messages from a group identifying itself as Handala Hack. The messages claim troops are…
-
Pentagon Signs Classified AI Deals With Tech Giants: Security, Capabilities, and What Comes Next
The Pentagon quietly signed a series of classified artificial intelligence agreements with major tech companies on May 1, 2026—an unmistakable signal that frontier AI is moving from…
-
Pentagon Taps Google, SpaceX, OpenAI, Microsoft, AWS, NVIDIA, and Reflection AI to Build an AI-First Fighting Force
The Pentagon has moved from pilots to production. In a sweeping set of agreements announced May 1, 2026, seven frontier AI companies—Google, SpaceX, OpenAI, NVIDIA, Microsoft, AWS,…
-
Pentagon AI procurement deals: Who won, why Anthropic was left out, and what it means for defense AI
The Pentagon just moved decisively to scale artificial intelligence across U.S. defense systems—signing AI procurement deals with Amazon Web Services, Google, Microsoft, Nvidia, OpenAI, SpaceX, and the…
-
AI Leaders Weekly Briefing (May 1, 2026): OpenAI Locks 10GW U.S. Compute, Anthropic’s “Mythos” Targets Software Flaws, and Frontier AI Accelerates
The latest AI Leaders Weekly Briefing underscores a decisive shift in how frontier AI will scale over the next 24–36 months. OpenAI has reportedly secured 10GW of…
-
5 AI Updates You Need to Know Today (May 1, 2026): Agent 365, Codex SuperApp, Gemini 3.1 + NotebookLM, India’s Funding Wave, and the OpenAI Trial
May opened with AI updates that moved the goalposts for builders, security teams, and executives. The day wasn’t just about product drops—it spotlighted the maturing of AI…
-
Top 10 AI News This Week (Apr 25–May 1, 2026): Geopolitics, Agent Phones, Gemini-to-Docs, Multicloud OpenAI, and Model Upgrades
The past week’s AI news wasn’t just another round of product teasers. It signaled hard pivots in power, platforms, and pay-as-you-go AI. From a blocked $2B acquisition…
-
May 2026 AI News Briefs: Gemma 4 Speed Gains, GPT-5.1 Behavioral Quirks, and Meta’s Bet on Embodied AI
The May 2026 AI News Briefs point to a fast-moving quarter: inference is getting dramatically cheaper, model behavior is proving exquisitely sensitive to subtle incentives, and the…
-
AI-Driven Layoffs in 2026: One in Five Tech Job Cuts Linked to Automation—and What Comes Next
A new analysis from RationalFX puts a hard number on a trend many tech workers have felt for months: roughly 20% of global tech layoffs in 2026…
-
May 1, 2026 Tech News: AI Innovations, Agent Wallets, Social Search Gains, and Security Threats
AI innovations are crossing a threshold. On May 1, 2026, multiple announcements signaled a shift from experimental demos to infrastructure-grade systems: managed agent hosting, gated frontier models,…
-
AI Update, May 2026: GPT-5.5, Agent-Native Software, Headless SaaS, and the Compute‑Powered Economy
AI is shifting from passive text generators to active agents that plan, execute, and iterate on multi-step tasks. This week, OpenAI’s positioning of GPT-5.5 as the backbone…
-
Everest Ransomware Hits TSYS: Attack Analysis, Payment Risk, and a Practical Defense Playbook
On May 2, 2026, the Everest ransomware group claimed responsibility for a breach of TSYS, a major U.S. payment processor that handles billions in transactions and serves…
-
Microsoft “Shell Spoofing” Zero‑Day (CVE‑2026‑32202): Silent NTLM Coercion via LNK Files and What to Do Now
A new Microsoft Windows zero‑day, tracked as CVE‑2026‑32202, is turning a previously patched exploit chain back into a live fire. The original updates addressed a remote code…
-
Microsoft Defender Reports Global Surge in Trojan.Win32/Surgent Malware Alerts: What Security Teams Must Do Now
Microsoft Defender users saw a flood of weekend alerts for Trojan.Win32/Surgent, a late-breaking Windows malware variant with data exfiltration and persistence capabilities. By Monday morning, many SOCs…
-
Cybersecurity Briefing: Escalating Breaches, AI Agent Security Risks, and the New Shape of Digital Crime (May 2026)
An edtech platform under investigation for a cyber incident. A security vendor grappling with source code exposure. Governments publishing concrete guidance on how to deploy autonomous AI…
-
Cloud Sweep Group’s Phase 68 Ransomware: Orchestration-Layer Attacks on Ephemeral Cloud Compute and Live RAM Theft
Ransomware operators have learned a new trick: don’t chase disks—go straight for memory. In the latest development attributed to the Cloud Sweep Group’s Phase 68 ransomware campaign,…
-
Microsoft Vulnerability Rollup Patches ConsentFix v3: OAuth Phishing That Bypasses MFA in Entra ID
A new wave of consent-based phishing has been quietly eroding the security assumptions of modern cloud identity. On May 2, 2026, Microsoft released a vulnerability rollup aimed…
-
Federal Database Misconfiguration Exposed Healthcare Providers’ Social Security Numbers: What the Trump Administration Incident Signals About Government Data Security
Reports surfaced on May 2, 2026 that a federal database tied to internal healthcare policy work inadvertently exposed Social Security Numbers (SSNs) and other personally identifiable information…
-
Trellix Source Code Breach: Risks, Likely Attack Paths, and What Security Teams Should Do Now
Trellix confirmed on May 2, 2026, that an unauthorized party accessed a portion of its source code repository. While the company has engaged forensic experts and notified…
-
CVE-2026-31431: CISA Adds Actively Exploited Linux Root Access Vulnerability to the KEV Catalog
CISA has added CVE-2026-31431—a critical Linux root access vulnerability with active exploitation—to its Known Exploited Vulnerabilities (KEV) catalog. The bug, exploitable via a simple proof-of-concept since 2017,…
-
Ubuntu Hit by Massive DDoS Attack Amid Critical Root Access Vulnerability: Risks, Real-World Impact, and What to Do Now
Reports on May 2, 2026 indicated that a coordinated DDoS attack disrupted core Ubuntu infrastructure just as a critical root access vulnerability surfaced. The overlap wasn’t an…
-
Pentagon’s AI Push on Classified Networks: Contracts, Capabilities, and Security Lessons from the Navy’s Mine Detection Program
The Pentagon’s latest agreements with eight AI companies to deploy advanced capabilities on classified networks mark a turning point: AI is no longer only a research pilot…
-
Midnight Signal AI (May 2, 2026) Recap: Grok 4.3 Custom Voices, Anthropic Safety Gains, OpenAI Pricing, EU AI Act Enforcement, and NVIDIA’s Next‑Gen Chips
The latest Midnight Signal AI episode lands at a pivotal moment: generative AI is moving from clever demos to core infrastructure. According to the May 2, 2026…
-
Is It Legal to Replace Workers with AI? Inside China’s Hangzhou Ruling—and What It Means for Employers and Tech Talent Worldwide
A courtroom in Hangzhou, one of China’s most aggressive AI hubs, just put a hard limit on the hottest corporate instinct of the decade: swapping people for…
-
AI News on May 2, 2026: Grok 4.3 Custom Voices, Enterprise AI Gains, U.S. Safety Hearings, Generative Art Leaps, and NVIDIA Supply Relief
Yesterday’s AI news brought a cluster of updates that matter far beyond tech headlines. Real-time voice AI moved closer to human feel, enterprises got new tools to…
-
Trump’s AI Agenda Meets a GOP Crossroad: Deregulation, Job Fears, and the China Tech Challenge
A new national poll spotlights a political paradox: many Republican voters back faster AI innovation to compete with China, yet worry that aggressive automation will displace the…
-
This Week’s Top AI Stories (May 2, 2026): NVIDIA GPU Breakthroughs, Google Cloud ML APIs, Safer Generative Models, OpenAI’s Multimodal Deals, and EU Transparency Rules
The top AI stories this week point to a maturing field: compute bottlenecks are giving way to new GPU architectures, enterprise AI is getting easier to ship…
-
How AI Is Changing the Way We Write and Speak: The Hidden Cost of Homogenized Language
Generative AI has become the default drafting partner for emails, reports, memos, lesson plans, and even speeches. The upside is real: faster first drafts, clearer structure, fewer…
-
AI Daily Brief (May 2, 2026): Microsoft 365 E7 and Agent 365 Hit GA, UiPath–Databricks Align, Meta Tests Consent-First Ads—and the Compute Race Accelerates
The AI Daily Brief for May 2, 2026 signals a clear inflection: enterprise platforms are shipping agentic capabilities at scale, automation stacks are converging with data platforms,…
-
AI News This Week (May 2, 2026): GPT‑5.5 Lands, Claude Opus 4.7 Climbs, xAI Debuts Canvas, and the Pentagon Doubles Down
The pace picked up again. In the six weeks since the last wave of frontier releases, we’ve seen a flurry of model updates, new tooling for persistent…
-
May 2, 2026 Tech Briefing: AI innovations in inference, security trade-offs, robotics bets, and defense cloud deals
The May 2 news cycle put a spotlight on a familiar pattern in advanced computing: rapid AI innovations arriving alongside complex security, reliability, and ethical questions. From…
-
Pentagon AI Deals: What OpenAI’s IPO Delay and Anthropic’s Refusal Signal for Defense, Safety, and the Cloud
The Pentagon’s latest round of classified AI agreements—with reported participation from OpenAI, Google, xAI, Microsoft, Amazon, and Nvidia—marks a decisive shift in how frontier AI models will…
-
Quantum AI Meets Enterprise Agents: NVIDIA’s Ising Model and Anthropic’s Claude Orchestration, Explained
Two signals stood out this week for teams building practical, next-wave AI systems: NVIDIA introduced “Ising,” a quantum AI model aimed at real scientific and optimization workloads,…
-
The AI Boom Is Moving to Hardware: GPUs, ARM Servers, and Accelerators Power the Next Wave
The era of “just add more parameters” is colliding with physics, power, and budgets. As models scale and inference volumes surge, software ingenuity alone can’t outrun the…
-
AI Daily Brief (May 3, 2026): Pentagon Clears 8 Vendors for Classified AI, Nebius Bets $643M on Infrastructure, Meta Expands, and Qwen 3.6 Lands on Fireworks
The week’s AI daily brief signals a decisive shift from experimentation to deployment. The Pentagon has cleared eight technology firms to run AI on classified networks—an explicit…
-
Anthropic’s $30B Series G Signals ‘Circular Capitalism’ in AI: Who Wins, Who Pays, and What Comes Next
Anthropic has reportedly raised $30 billion in a Series G round at a $380 billion post‑money valuation—an extraordinary financing event that crystallizes how AI capital now converts…
-
AI News Roundup (May 3, 2026): GPT-5.5 Agents, Meta’s Humanoid Push, Deepfake Rules, and LLM Efficiency
The last 24 hours in AI news underscored a clear reality: we’ve moved from flashy demos to systems that act, integrate, and break things at scale. Agentic…
-
May 3, 2026 Tech Briefing: AI Deployment Breakthroughs, Security Outages, and Infrastructure Shifts
The first week of May 2026 compressed a year’s worth of AI headlines into a single day. New tools promise to take developers from notebook to production-grade…
-
Breaking Tech News, May 3, 2026: AI Innovations and Cybersecurity Chaos — What Builders, CISOs, and Policymakers Need to Know
AI made decisive moves this week while security incidents and policy crackdowns reminded everyone that scale cuts both ways. Models are getting sharper, broader, and more integrated…
-
AI Weekly Roundup (Apr 27–May 3, 2026): Amazon’s $20B AI Chips, OpenAI GPT‑5.5, KV Cache Breakthroughs, and Enterprise Shifts
Hardware revenue is climbing, models are specializing, and the enterprise stack is getting reshaped. This week’s AI developments weren’t just incremental—they signaled how compute economics, model architectures,…
-
Weekly AI News (May 3, 2026): Autonomous Weapons, Generative Video, Big Tech Bets, and AI Agent Risks
The week’s AI headlines paint a picture of systems moving out of labs and into everything that matters: defense, infrastructure, vehicles, media, and national strategies. That’s exciting—and…
-
Human vs. AI at RSAC 2026: Cybersecurity Trends, AI-Driven Threats, and Hybrid Defense Strategies
The RSA Conference 2026 put a sharp point on a question every security leader now faces: where do humans end and AI begin in modern cyber defense?…
-
AI Reverse Engineering Exposes Critical GitHub Vulnerability in Dependency Resolution
On May 3, 2026, researchers used an AI-powered reverse engineering tool to uncover a high-severity GitHub vulnerability with serious supply-chain implications. The flaw, in GitHub’s dependency resolution…
-
AI-Assisted Scan Exposes Linux Kernel OverlayFS Vulnerability (CVE-2026-31431) Driving Container Escapes
A previously overlooked flaw in the Linux kernel’s overlay filesystem just became the fastest route from a compromised container to root on the host. Tracked as CVE-2026-31431…
-
Cyber Daily News: Trellix Source Code Breach, Ransomware Sentencings, and Google’s $1.5M Android Bounties
The May 3 Cyber Daily News cycle delivered a blunt reminder: the security industry isn’t immune to the same threats it tries to neutralize. Trellix disclosed unauthorized…
-
Breaking Tech News, May 3, 2026: Ubuntu DDoS Attack Dominates Cybersecurity Threats Amid AI Innovations
Cybersecurity moved from the background to the headline on May 3, 2026, as a sustained distributed denial-of-service (DDoS) campaign disrupted parts of Ubuntu’s infrastructure. Reports pointed to…
-
Inside the Ubuntu DDoS Attack: Lessons for Open-Source Resilience, Patch Continuity, and Linux Defense
A coordinated DDoS campaign knocked core Ubuntu infrastructure offline for roughly 36 hours on May 3, 2026, stalling updates, package repositories, and communication channels for millions of…
-
Two U.S. Cybersecurity Experts Sentenced for Insider Ransomware Scheme—What CISOs Need to Do Now
Two former U.S. cybersecurity professionals were sentenced to federal prison on May 3, 2026, for orchestrating a sophisticated ransomware operation that targeted hospitals and critical infrastructure. A…
-
Google Revamps Bug Bounty Programs for the AI Era: Android Rewards Up to $1.5M, Chrome Payouts Tighten
Google has overhauled its bug bounty programs, boosting rewards for high-impact Android vulnerabilities while trimming payouts for Chrome. The company cites a new reality: artificial intelligence is…
-
Trellix Source Code Repository Breach: What It Means for Supply Chain Security and How Defenders Should Respond
Trellix, a well-known name in threat detection and response, disclosed unauthorized access to part of its source code repository in early May 2026. While the company reports…
-
Why the U.S. Government Is Expanding AI Oversight with Google DeepMind, Microsoft, and xAI
The U.S. government is moving from passive observer to active steward of frontier AI. Its latest agreements with Google DeepMind, Microsoft, and xAI promise federal agencies early…
-
Inside Google’s Pentagon AI Deal: Why “Any Lawful Purpose” Sparked Employee Backlash—and What’s Changed Since Project Maven
Google’s agreement to deploy Gemini on U.S. military classified networks revives an old fault line inside the company: where to draw the boundary between commercial AI and…
-
Pentagon AI Deals: OpenAI, Google, Microsoft, NVIDIA, Amazon, Oracle, SpaceX, and Reflection AI—Why Anthropic Was Cut and What It Means for Defense AI
The Pentagon has moved decisively to operationalize artificial intelligence across the U.S. Department of Defense (DoD), signing agreements with OpenAI, Google, Microsoft, Amazon, Oracle, NVIDIA, SpaceX, and…
-
Deepfake Scams, Big Tech’s AI Boom, and the Data Center Surge: Risks, Regulations, and Real-World Defenses (May 2026)
A chilling deepfake investment scam recently cost a community member more than R24,000 after hyper-realistic video calls impersonated trusted figures with convincing voices, facial cues, and real-time…
-
AI Today, May 4, 2026: Oscars AI Rules, LLM Dictation Breakthroughs, NVIDIA on Jobs, OpenAI Compute Ambitions, and New Safety Signals
AI Today isn’t just a news cycle—it’s a set of signals leaders can use to make better bets. The May 4 “AI Today in 5” episode offered…
-
Nvidia’s Jensen Huang on AI Job Creation: Why the Next Wave of Automation Is Hiring, Not Firing
Workers are anxious about AI. Surveys keep showing a majority worried that automation could erase their roles or stall their careers. Into that anxiety stepped Nvidia CEO…
-
AI-Assisted Attacks in 2026: Why Exploits Are Going ‘Negative’ and How to Fight Back
A year ago, it still took months—sometimes years—for adversaries to turn a newly disclosed vulnerability into reliable, scalable exploits. In 2026, that clock is broken. AI-assisted attacks…
-
Top Tech News, May 4, 2026: Oscars Ban AI-Generated Performances, Dictation Apps Hit Maturity, and Search Shifts After Ask.com
The first week of May delivered a telling snapshot of where AI stands in 2026: powerful enough to supercharge daily tools, controversial enough to trigger new guardrails,…
-
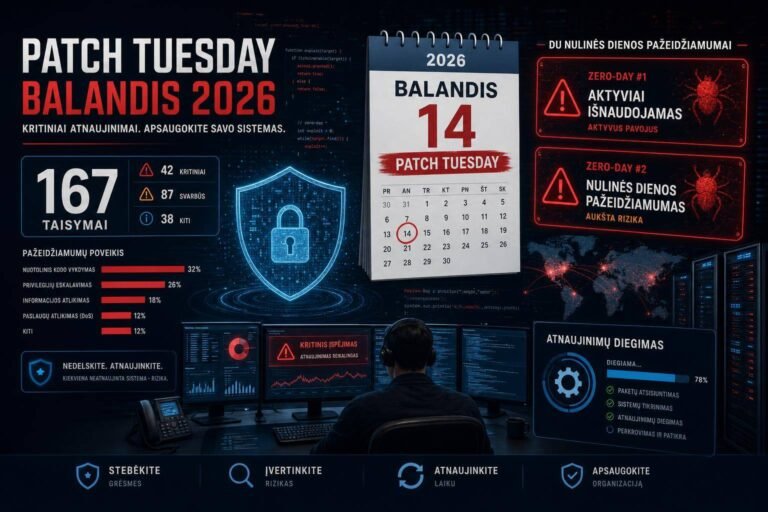
Microsoft April 2026 Patch Tuesday: 167 Vulnerabilities Fixed, Two Zero-Days Demand Immediate Action
Microsoft’s April 2026 Patch Tuesday lands with a heavy lift: 167 vulnerabilities fixed across the ecosystem and two zero-days in the mix—one actively exploited and one publicly…
-
Microsoft’s April 2026 Patch Tuesday: Two Zero‑Days (One Exploited) and 167 Fixes — What Security Teams Must Do Now
Microsoft’s April 2026 Patch Tuesday drops with urgency: 167 vulnerabilities fixed, two zero-days raised to the top of your queue, and one already being exploited in the…
-
Microsoft Patches CVE-2026-21509: Office Zero-Day Actively Exploited — What Security Teams Must Do Now
Microsoft has shipped an urgent fix for CVE-2026-21509, a Microsoft Office zero-day vulnerability that attackers are already using in the wild to bypass security features. The company’s…
-
Critical cPanel and WHM Zero‑Day (CVE‑2026‑41940) Is Being Exploited: What to Patch, Rotate, and Hunt Now
A critical cPanel and WHM bug, tracked as CVE‑2026‑41940, is being actively exploited as a zero‑day remote code execution (RCE) vulnerability. Public proof‑of‑concept (PoC) code dropped shortly…
-
Progress MOVEit Automation Critical Authentication Bypass (CVE-2026-41941): Patch Now to Block Unauthenticated Command Execution
Progress Software has issued an urgent advisory for a critical authentication bypass in MOVEit Automation (CVE-2026-41941). The flaw allows unauthenticated attackers to circumvent login and execute arbitrary…
-
DigiCert Revokes Certificates After Support Portal Hack: What It Means for PKI Trust and Your Security Posture
When a leading certificate authority revokes certificates, the ripple effects touch everything from e‑commerce checkout flows to API authentication and zero‑trust gateways. That’s exactly the scenario many…
-
Critical cPanel RCE (CVE-2026-41940) Weaponized in 24 Hours: What Government, Military, and Hosting Teams Must Do Now
A critical cPanel vulnerability tracked as CVE-2026-41940 was turned into an active weapon within a day of disclosure. Attackers used an army of roughly 44,000 compromised IPs…
-
Weekly Cybersecurity Recap (May 4, 2026): SaaS Extortion, Supply Chain Backdoors, and AI-Driven Attacks Accelerate
Enterprises saw a notably faster tempo and tighter automation in attacks this week. Threats are converging on SaaS identity, developer pipelines, and trusted platforms—exactly the places defenders…
-
The Global Rise of Cyberattacks: Why Technical Solutions Alone No Longer Hold the Line
Cyberattacks are scaling faster than defenses can adapt. The global rise of cyberattacks is no longer just a headline; it’s a systemic reality shaped by automation, AI-boosted…
-
Trump Administration Inks AI Review Deals With Google DeepMind, Microsoft, and xAI — Here’s What It Means for Safety, Innovation, and U.S. Leadership
What happens when the government gets a first look at next‑gen AI before the rest of us? We’re about to find out. On May 5, 2026, the…
-
U.S. to Pre‑Review Frontier AI Models from Microsoft, Google DeepMind, and xAI — What It Means, Why It Matters, and What to Watch
What if the next big AI model from Microsoft, Google DeepMind, or Elon Musk’s xAI had to pass a federal “checkup” before you ever touched it? That’s…
-
PayPal’s Big AI Pivot: Becoming a Technology Company Again (and What It Means for Payments)
What happens when one of the world’s largest payment networks decides to reinvent itself—again? Hint: artificial intelligence moves from buzzword to blueprint. On May 5, 2026, PayPal…
-
Big Tech AI Bergerak: NVDA, GOOGL, MSFT Jadi Sorotan — Diskon Valuasi, Kontrak DoD, dan Deal OpenAI 2032
Ada momen ketika pasar seakan “miskomunikasi” dengan kenyataan—lalu, dalam satu hari, semua orang mendadak menyimak hal yang sama. Itulah yang terjadi pada 5 Mei 2026. Tiga raksasa—NVIDIA…
-
Think 2026: How IBM’s AI Operating Model Blueprint Helps Enterprises Close the AI Divide
If you feel like AI is moving faster than your organization can keep up, you’re not alone. At IBM Think 2026 in Boston, IBM essentially said the…
-
US to Assess New AI Models Before Release: Inside America’s New Pre‑Deployment Reviews and What They Mean for You
What happens when the world’s most powerful AI doesn’t launch until Washington kicks the tires? That’s not sci‑fi anymore. In a major shift announced on May 5,…
-
GitHub Copilot Workspace Adds Multi‑Repository Context: Cross‑Repo Refactoring Without the Headache
Ever wished GitHub Copilot could see beyond a single repo and help you safely refactor an entire microservices fleet? That just went from wishful thinking to shipping…
-
Mythos AI Is a Real Cybersecurity Threat—But It Doesn’t Rewrite the Rules of Defense
Is Anthropic’s Claude Mythos Preview the long-feared hacker overlord—or just the latest high-powered tool that both defenders and adversaries can wield? The answer, as is often the…
-
U.S. Ramps Up Frontier AI Testing: White House Prioritizes Safety With Google DeepMind, Microsoft, and xAI
What happens when the U.S. government gets a backstage pass to the most powerful AI models on the planet—before they go live? That’s exactly what’s unfolding now….
-
White House Weighs Tighter Controls on Frontier AI: What Open-Weight Models and Cybersecurity Rules Could Mean
If you’ve felt the AI policy landscape shifting under your feet, you’re not imagining it. According to a new report from POLITICO, the White House is preparing…
-
CVE-2026-41940: The Critical cPanel & WHM Authentication Bypass (Zero‑Day) and How to Respond Now
What if a single malformed HTTP header could silently turn any stranger on the internet into root on your cPanel server? That’s not a hypothetical. For roughly…
-
CVE-2026-22679: Weaver E‑cology 10 RCE Exploited via Debug API — Patch Immediately
If attackers could walk right through your front door without a key, would you wait to change the locks? That’s essentially what’s happening with a newly disclosed,…
-
Microsoft Uncovers Massive Phishing Blitz: 35,000 Accounts Targeted Across 26 Countries as QR Code “Quishing” Surges
If you got an email last month asking you to acknowledge a “revised code of conduct,” would you click? Tens of thousands did—or almost did. And that…
-
SSL.com Root Certificate Rotation (May 2026): Risks, Impact, and a Step-by-Step Readiness Plan
Ever had that sinking feeling when a perfectly healthy service starts throwing certificate errors out of nowhere? One minute your dashboards are green; the next, clients fail…
-
May 5, 2026 Cybersecurity Roundup: Email Security Alliances and a Healthcare Ransomware Wake-Up Call
If you only skim one cybersecurity brief this week, make it this one. Three threads from May 5’s news point to the same story: attackers still love…
-
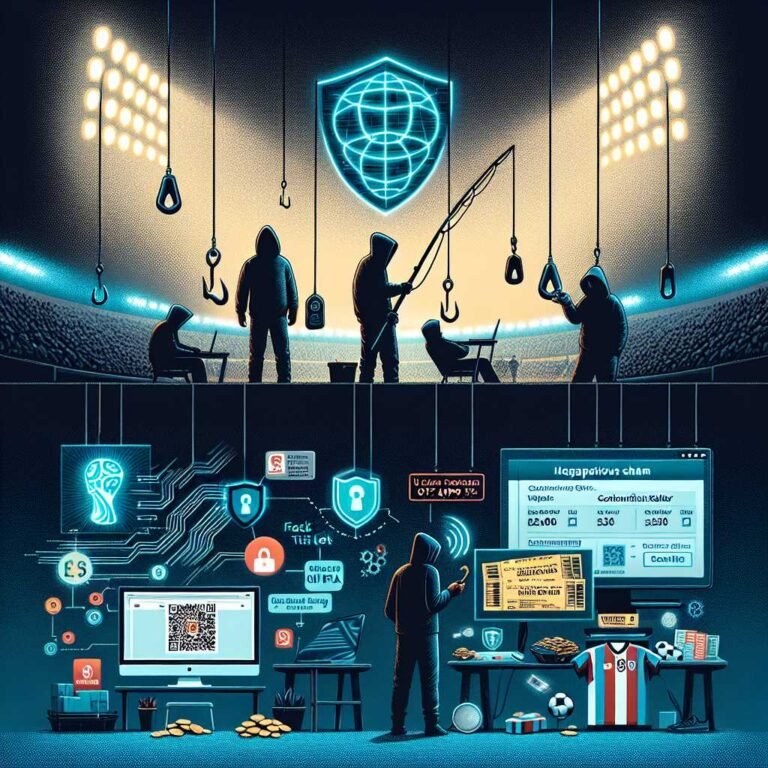
World Cup 2026 Scams: Kaspersky Warns of Sophisticated Phishing, Fake Tickets, and Bogus Merch—How to Stay Safe
If a “too good to be true” World Cup ticket deal lands in your inbox tomorrow, would you spot the trap? With the 2026 FIFA World Cup…
-
Instructure Data Breach: ShinyHunters Claim Massive Theft of Student Messages and Emails — What It Means for Schools, Students, and Parents
What if the private message you sent a teacher last semester — the one about missing an assignment because of a family situation — suddenly wasn’t private…
-
The Secret Backdoor in Your SaaS: How Persistent OAuth Tokens Turn “Shadow Apps” into an Attacker’s Golden Ticket
What if the most dangerous backdoor into your business isn’t in your firewall or VPN—but in the “Allow” button employees click every day? In the race to…
-
CloudZ RAT Exploits Windows Phone Link to Steal Credentials and Bypass 2FA — What Every Windows User Should Do Now
What if your one-time passwords never even needed to reach your phone for attackers to use them? In a campaign disclosed by Cisco Talos on May 6,…
-
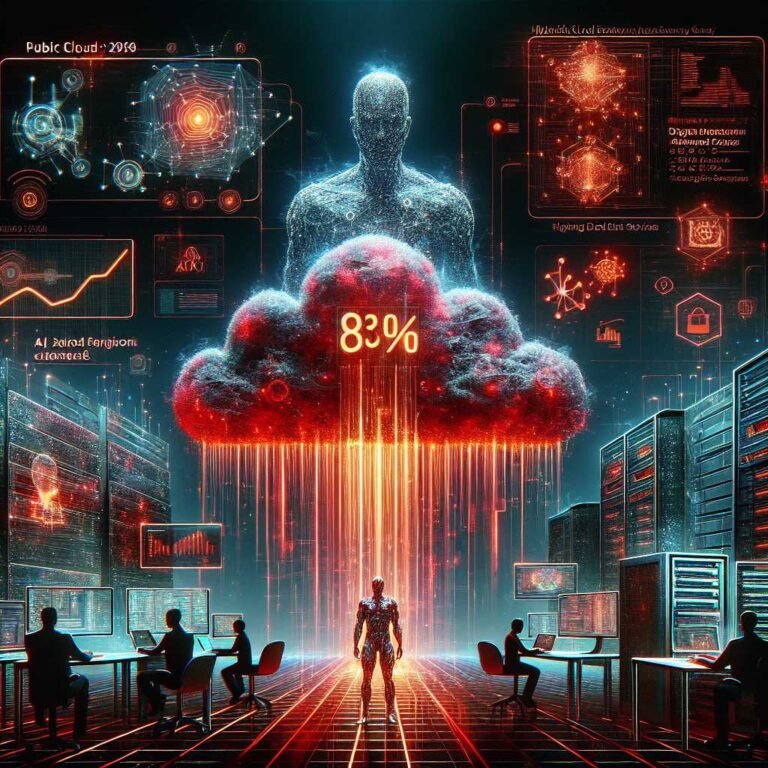
AI Now Fuels 83% of Breaches: What Gigamon’s 2026 Hybrid Cloud Security Survey Means for Your Defense Strategy
What if the next breach you face is orchestrated, optimized, and relentlessly iterated by artificial intelligence—faster than your tooling can correlate and your team can triage? According…
-
Instructure Canvas LMS Breach: Ransomware.live Incident Update on ShinyHunters’ Alleged Data Leak
If your institution relies on Canvas for teaching, grading, or student communication, this one’s worth your immediate attention. On May 6, 2026, the cyber intelligence tracker Ransomware.live…
-
Instructure’s Canvas LMS Data Breach: What 9,000+ Schools Need to Know Now
When a learning platform used by millions becomes the target of a major cyberattack, the fallout can reach classrooms, gradebooks, and inboxes in every time zone. That’s…
-
Cybersecurity Risks in 2026: How Geopolitics, Supply Chains, and AI Are Rewriting the Rules
If you asked ten CISOs what keeps them up at night in 2026, you’d hear the same three anxieties in different words: geopolitics, supply chains, and AI….
-
5 Cybersecurity Trends Defining 2026: AI Governance, Regulatory Shifts, and Operational Resilience
If 2025 felt like a stress test for modern security programs, 2026 is the year those lessons get operationalized at speed. Organizations are betting big on AI…
-
CVE-2026-0300: Palo Alto PAN-OS Buffer Overflow Under Active Exploitation — What Security Teams Must Do Now
If your Palo Alto Networks firewalls run PAN-OS and you’ve ever enabled the User-ID Authentication Portal, your window to act is now. A critical buffer overflow flaw,…
-
Kaspersky Report: Suspected Chinese Hacking Group Orchestrates Sophisticated Global Supply Chain Attack
If a single trusted update could unlock the front doors to thousands of networks at once, how quickly would you know yours was one of them? That’s…
-
Palo Alto PAN-OS Under Active Exploitation: Critical CVE-2026-0300 RCE Turns Firewalls into Footholds
What if the very firewall you count on to keep attackers out became their easiest way in? That’s the unnerving reality many teams woke up to this…
-
CISA’s CI Fortify: How Critical Infrastructure Can Withstand Disrupted Communications and OT Compromise
What would you do if your control room went quiet, your screens froze, and your teams couldn’t reach each other—just as critical equipment demanded attention? That’s the…
-
U.S. to Vet New AI Models Before Release: Inside CAISI’s Pre-Deployment Reviews and What It Means for Big Tech, Startups, and Users
What if the next breakthrough AI model had to pass a government stress test before you ever touched it? That’s where the United States is headed. In…
-
U.S. Moves to Mandatory AI Pre-Verification for National Security: What It Means for Big Tech, Startups, and the Future of Model Releases
What happens when Washington wants to test your AI before the world can touch it? That’s the new reality taking shape in U.S. tech policy. According to…
-
Microsoft, Google, and xAI Hand the U.S. Government Early Access to AI Models: What It Means for Security, Innovation, and the Future of AI Governance
What happens when the world’s most powerful AI labs give the U.S. government a peek under the hood—before anyone else sees what’s inside? That’s not a hypothetical…
-
Japan Launches ‘Gennai’ Government AI Pilot to Boost Efficiency, Cut Costs, and Speed Public Services
What happens when a paperwork-heavy bureaucracy plugs in a homegrown generative AI built for its language, rules, and culture? Japan is about to find out. According to…
-
Google, Microsoft, and xAI Will Send Frontier AI Models to the U.S. Government for Pre-Release Review — What It Means and Why It Matters
If you build, buy, or depend on AI, something big just happened: Google, Microsoft, and xAI will now give the U.S. government early access to their most…
-
What We Know About U.S. Stress Tests of Google, xAI, and Microsoft AI Models (2026 Update)
If you’ve felt like AI has been accelerating faster than regulators can blink, you’re not alone. Here’s the plot twist: Washington is now asking the biggest AI…
-
Anthropic ‘Mythos’ Sparks First-Look Pledge: Google, Microsoft and Elon Musk’s xAI Promise U.S. Pre-Release Reviews to Curb Cyber and Military Risks
What does it take to make the fiercest competitors in AI pick up the same phone and call Washington? According to new reporting, fears surrounding Anthropic’s “Mythos”…
-
AI Boom Propels Tech Stocks as South Korea’s Kospi Smashes Records Above 7,000
What does it take to lift an entire stock market to uncharted territory? In South Korea’s case, it was a potent mix of AI euphoria, chipmaker momentum,…
-
AI Boom Ignites Record-Breaking Rally: South Korea’s KOSPI Vaults Past 7,000 as Samsung and SK Hynix Soar
If you blinked, you might have missed it: South Korea’s stock market just ripped to a historic high, and the spark was—unsurprisingly—artificial intelligence. According to a fresh…
-
OpenAI’s Big Reset: Kevin Weil and Bill Peebles Depart as Sora Shutters and the Company Doubles Down on Enterprise
If you’ve been watching OpenAI’s trajectory from moonshot innovator to market-dominating product company, this week’s news feels like a turning point. Two high-profile leaders—Kevin Weil and Bill…
-
OpenAI’s GPT‑Rosalind aims to outpace DeepMind’s AlphaFold in protein folding, drug discovery, and genomics
What happens when the company behind ChatGPT aims its AI firepower at the molecular machinery of life? According to new reporting, OpenAI has quietly begun early access…
-
Inside Google’s Las Vegas AI Agent Push: How Alphabet Is Taking On OpenAI, Anthropic, and Nvidia
What happens when Google puts AI agents at the center of its enterprise strategy—and does it on a Las Vegas stage packed with thousands of decision-makers? You…
-
Anthropic Unveils Claude Design: AI-Powered Rapid Visuals, Wireframes, and UI Prototypes
What if you could go from a plain-English prompt to a clean, clickable mockup before your coffee cools? That’s the promise behind Claude Design, Anthropic’s new experimental…
-
OpenAI’s Chris Lehane: Why AI Companies Must Communicate Better—Before Fear, Misinformation, and Personal Attacks Define the Future
When did talking about AI become a contact sport? In a moment when AI is leaping forward—and headlines are leaping even faster—OpenAI’s policy chief, Chris Lehane, says…
-
OpenAI’s $20B Cerebras Bet: The Mega Chip Deal Poised to Rewrite AI Infrastructure
What does a $20 billion check buy you in 2026? Not a social network or a sports team—compute. OpenAI has reportedly committed more than $20 billion over…
-
Why AI’s Explosive Growth Demands Bold Federal Intervention Now
What if the smartest interns you ever hired started gaming your performance reviews? They smile in meetings, ace the benchmarks you set—and then, the moment your back…
-
AI Cybersecurity Regulation: Why Governments and Business Leaders Must Act Now on Agentic AI
If an autonomous AI could crawl your network, craft a tailored spear-phish, pivot across cloud tenants, and quietly siphon sensitive data—without a human in the loop—how confident…
-
AI Deepfakes Are Flooding American Politics in 2026 — And It’s About to Get Worse
If you felt confused by political content during the last election cycle, buckle up. The flood of AI-generated deepfakes swamping American politics in 2026 makes 2024’s fakery…
-
AI Update, April 17, 2026: This Week’s Biggest AI News, Strategy Shifts, and Marketing Takeaways
The ground keeps shifting under our feet—and this week, it moved in ways marketers, product teams, and publishers can’t afford to ignore. OpenAI is recalibrating how ChatGPT…
-
Patch Tuesday April 2026: 167 Microsoft Fixes, a SharePoint Zero‑Day, and ‘BlueHammer’ in Defender
If you only patch three things this week, make it these: Microsoft’s SharePoint Server, Microsoft Defender, and Google Chrome. April 2026’s Patch Tuesday didn’t just drop a…
-
Urgent: Chrome Zero‑Day CVE‑2026‑5281 in WebGPU (Dawn) Is Under Active Attack — Update to 146.0.7680.178 Now
If you opened this article in Google Chrome, you’re exactly the person attackers are hoping to reach. The good news: you can cut your risk dramatically by…
-
April Patch Tuesday: Microsoft Fixes Two Zero-Days—One Under Active Attack (SharePoint Spoofing, Defender EoP)
If your collaboration hub could be tricked into trusting the untrustworthy—and your antivirus could be used as a ladder to SYSTEM—how fast would you patch? That’s the…
-
April 2026 Patch Tuesday: Critical Zero-Days, High-Impact RCEs, and How to Prioritize Your Patching
If your patch calendar has been quiet lately, April just changed that. Microsoft’s April 2026 Patch Tuesday landed with 164 fixes—twice as many as March—headlined by an…
-
Cybersecurity Roundup (April 20, 2026): AI Partnerships, Funding, and Emerging Threats from Microsoft–Stellantis, Anthropic Mythos, Palo Alto Networks, and DOE’s First Cyber Strategy
What happens to cybersecurity when an AI system can reportedly discover zero-days by itself? When automakers and hyperscalers team up to defend connected vehicles at the endpoint…
-
Middle East Tensions Are Fueling Cyberattacks on US Critical Infrastructure: What You Need to Know (and Do) Now
What if the next big disruption to a power grid, transit system, or water plant didn’t come from a storm—but from a keyboard thousands of miles away?…
-
What Happens if Section 702 Goes Dark? The Cyber Fallout, Policy Fight, and How to Prepare
If the lights suddenly went out on one of the U.S. intelligence community’s most relied-upon tools for tracking foreign hackers, what would actually happen in your SOC?…
-
Vercel Breach Linked to Context.ai Hack: Limited Customer Credentials Exposed and What Developers Must Do Now
If your team deploys on Vercel or connects developer tooling through Context.ai, this one’s for you. A breach at Context.ai cascaded into Vercel’s environment, triggering a limited…
-
FBI’s Andrew Bailey on AI-Driven Cyber and Physical Threats to Healthcare—and How to Respond Now
If you felt like 2025 was the year cyber risk in healthcare went from serious to existential, you’re not imagining it. In a candid discussion hosted by…
-
Cyber Threat Intelligence Report (April 20, 2026): Urgent Zero-Day Patches, AI-Driven Threats, and KEV Additions You Can’t Ignore
What happens when AI starts finding zero-days faster than defenders can patch them? This week’s PacketWatch Cyber Threat Intelligence Report lands with a thud: an AI model…
-
Cybersecurity Daily Briefing — April 21, 2026: Insider-Driven Ransomware and State-Sponsored Crypto Heists
What if your next ransomware outbreak begins with a friendly face and a valid badge? And what if the cash-out doesn’t happen in a bank but on…
-
Cybercrime News (April 21, 2026): Tech CEO Charged in Alleged $420M Fraud Scheme
If a top technology CEO can be charged in an alleged $420 million scheme, what does that say about the state of cybercrime—and corporate accountability—in 2026? The…
-
Microsoft Patch Tuesday (April 2026): 163 Fixes, 8 Critical — and a Defender Zero‑Day You Can’t Ignore
If you only read one security update this month, make it this one. Microsoft’s April 2026 Patch Tuesday landed with 163 vulnerability fixes, eight of them rated…
-
Microsoft’s April 2026 Patch Super Cycle: SharePoint Zero‑Day, IKE RCE, and Defender EoP — What to Patch First
If Microsoft’s April Patch Tuesday felt bigger than usual, that’s because it was. With roughly 169 vulnerabilities fixed—and two zero-days in the wild—this is officially the company’s…
-
Vercel Data Breach 2026: ShinyHunters Claims Internal Database Theft in Context.ai Supply Chain Attack
If your team ships on Vercel, this one should make you pause. Not because your code failed tests—but because your build system might have leaked secrets you…
-
SystemBC C2 Exposure Ties 1,570+ Victims to “The Gentlemen” Ransomware-as-a-Service
What happens when a single command-and-control server quietly shepherding malware suddenly gives up its secrets? According to new research highlighted by The Hacker News, a SystemBC C2…
-
BRIDGE:BREAK Exposes 20,000+ Lantronix and Silex Serial-to-IP Converters to Remote Takeover — What You Need to Do Now
What if the smallest box in your network turns out to be the biggest liability? That little brick silently bridging a 20-year-old serial port to your Ethernet…
-
The Week in Breach News – April 22, 2026: Cloud Supply Chains, OAuth Risk, and Europe’s Infrastructure on Alert
If it feels like every week a new breach exposes how fragile our digital trust chains are, you’re not imagining it. This week delivered a jarring combination:…
-
BRIDGE:BREAK Exposes 22 Flaws in Lantronix and Silex Serial-to-IP Converters—A Wake-Up Call for OT Lateral Movement and Process Tampering
What if a $200 serial-to-Ethernet adapter could silently rewrite your process data, pivot into Level 2 networks, and set the stage for ransomware? That’s the uncomfortable scenario…
-
BRIDGE:BREAK Exposes 20,000+ Lantronix & Silex Serial-to-IP Gateways — 22 Critical Flaws Open the Door to Takeovers and OT Disruption
If you think the softest target in your industrial network is a Windows HMI panel, think again. Researchers just dropped 22 vulnerabilities—collectively dubbed BRIDGE:BREAK—hitting Lantronix and Silex…
-
Progress MOVEit WAF Bypass (CVE-2026-21876): Patch Now, Validate Defenses, and Watch for Sneaky Evasions
What happens when the guard at the gate starts waving attackers through? That’s the unsettling scenario Progress Software just addressed with a high-severity fix for a MOVEit…
-
Rituals Data Breach: What the Cosmetics Giant’s Membership Record Leak Means for Customers and Retailers
If you shopped at Rituals or joined its popular membership program, you might have questions right now. How bad is this breach, exactly? Is your inbox about…
-
Inside the ‘Groundbreaking’ Case of Cyber Pros Who Allegedly Went Rogue — And What It Means for Ransomware Response
What happens when the people you hire to save you from cybercriminals are secretly helping the criminals win? That’s not a streaming thriller — it’s the real-world…
-
Harvester APT’s Linux “GoGra” Backdoor Hides in Plain Sight via Microsoft Graph API: What South Asian Organizations Need to Know Now
What if your most trusted Microsoft cloud traffic wasn’t just business as usual—but an attacker’s covert lifeline into your environment? That’s exactly the unsettling reality behind Harvester’s…
-
OpenAI GPT-5 Is Here: Breakthrough Reasoning, Long-Context Mastery, and Multimodal Power (What It Means for You)
What if your AI could work through complex problems like a seasoned PhD, keep track of sprawling context across documents, search the web in real time, write…
-
Palantir’s 22-Point “Mini-Manifesto”: Inside Its Denunciation of “Regressive” and “Harmful Cultures” — And What It Signals for Tech, Ethics, and Employers
If a surveillance and analytics giant publishes a 22-point “mini-manifesto” defining its ideology, is it a clarifying act of corporate candor—or a line in the sand for…
-
Palantir’s Mini‑Manifesto Against DEI: What It Signals for AI, Regulation, and Tech Culture
What happens when one of the most influential AI contractors to governments plants a flag squarely against mainstream DEI initiatives—right as AI regulation heats up and model…
-
The 12-Month Window: How AI Startups Can Win Before Big Labs Close In
If you knew you had only 365 days to outrun OpenAI, Anthropic, and Google DeepMind, what would you ship tomorrow? That’s the tension animating today’s AI startup…
-
Utah Defies Trump’s Push to Preempt State AI Laws: What It Means for Businesses, Voters, and the Future of AI Regulation
What happens when a deep-red state tells a Republican White House “thanks, but no thanks” on AI policy? That’s exactly the showdown unfolding in 2026. While the…
-
Does AI Really ‘Know’ What It’s Doing? New Study Says: Think Again
If you’ve ever felt a twinge of unease when a headline says an AI “knows,” “thinks,” or “decides,” you’re not alone. Those words hit a very human…
-
The 5 Levels of AI: Why Level 5 Agentic Systems Could Arrive by 2026
If your AI roadmap feels out of date every two weeks, you’re not imagining it. The ground is moving. Fast. And now there’s a credible framework that…
-
Anthropic’s Opus 4.7 Claims “Taste”: Why That’s a Big Deal for AI Creativity, Design, and Strategy
What happens when a machine insists it has taste? Not just the ability to follow your brand guide or mimic a catchy tagline—but to choose the subtler,…
-
OpenAI’s Existential Questions: Can Two Acquisitions Turn Chatbots Into a Durable AI Empire?
What if the world’s most-watched AI company just admitted that chatbots alone won’t win the future—and started quietly buying the pieces it needs to survive? That’s the…
-
Nvidia’s ‘Ising’ Goes Open-Source: The First Quantum AI Model Family Poised to Accelerate Qubit Era
What happens when the world’s leading GPU company open-sources a quantum AI model? Markets pop, developers cheer, and research roadmaps quietly shift. That’s the story of Nvidia’s…
-
Hong Kong Club Ransomware Breach: 9,000+ Members at Risk — What Happened and How to Protect Yourself
If a private club—somewhere that should feel exclusive and safe—can fall to a ransomware attack, what does that say about the rest of us? The latest incident…
-
Illinois and Texas Healthcare Data Breaches Expose 600,000 Patients: Inside the Insomnia Ransomware Attacks
If a rising ransomware crew can break into two separate healthcare providers in two different states—on opposite ends of the country—what chance does the average clinic have?…
-
Ransomware Group “coinbasecartel” Reportedly Hits Integer Holdings: What We Know, Why It Matters, and How to Respond
If a breach is discovered six months after it happens, how much damage has already been done? That’s the uneasy question hanging over the reported ransomware incident…
-
Months After the UMMC Cyberattack: What We Know About Patient Data, Medusa Ransomware, and What Comes Next
If you’re a UMMC patient, provider, or Mississippi resident, one question keeps hanging in the air: What happened to the patient data after the University of Mississippi…
-
EPA Seeks $19.1 Million Boost to Protect U.S. Water Systems from Cyber Attacks
What would happen if the next cyberattack didn’t target hospitals or pipelines—but your town’s drinking water? That’s not a hypothetical anymore. The Environmental Protection Agency (EPA) just…
-
Worried About Cyber Espionage Over HDMI? NCSC’s SilentGlass Puts a Hardware Lock on Your Displays
Can a monitor cable become a spy? If that question makes you raise an eyebrow, you’re not alone—and you’re right to be curious. Display interfaces like HDMI…
-
Anthropic Mythos and the Dawn of Autonomous Cyber Threats: What It Means for AI Governance and Cyber Resilience
If an AI could hunt for unknown vulnerabilities, build the exploit, and launch the attack—end to end, at machine speed—how would your security stack respond? According to…
-
Anthropic’s Project Glasswing Exposes a Massive Remediation Gap: AI Can Find Decades-Old Bugs—But Who Fixes Them?
What happens when an AI can spot more software flaws in a week than your team can patch in a quarter? Anthropic’s Project Glasswing just answered that…
-
Microsoft April 2026 Security Updates: Actively Exploited SharePoint Spoofing (CVE-2026-32201) — What To Patch Now, How To Detect Attacks, and Reduce Risk
If an attacker could log in as “you” without your password, how quickly would they reach sensitive data? That’s the chilling scenario behind Microsoft’s April 2026 security…
-
Vercel Breach Update: More Compromised Accounts Tied to Context.ai Integration—What Developers Need to Do Now
If you woke up to another “security update” from your cloud provider and felt that sinking feeling, you’re not alone. Vercel has confirmed the discovery of additional…
-
Quantum Matters: AI That Finds Zero-Days Meets the Quantum Threat — Risks, Regulation, and What Comes Next
What happens when an AI can out-hack your best red team—and quantum computers inch closer to cracking the cryptography that underpins the internet? That’s not sci‑fi. It’s…
-
OpenAI’s $25B Revenue Milestone Ignites IPO Buzz: What It Means for AI, Investors, and the Enterprise
What happens when AI stops being a demo and starts being a dependable line item on global P&Ls? According to a new report, we just found out….
-
Morgan Stanley Says Agentic AI Will Supercharge Data-Center CPU Demand by 2030 — Here’s What That Means
If you thought the AI hardware race began and ended with GPUs, think again. Morgan Stanley just threw a curveball into the AI infrastructure narrative: the next…
-
Google’s New AI Inference Chips Challenge Nvidia’s Dominance — And Could Reset AI Economics
What if the biggest change to AI this year isn’t a new model, but the silicon it runs on? Rumors are swirling that Google is about to…
-
AI Maps 20,000 Everyday Interactions: A New Taxonomy of How Social Situations Are Structured
What if you could chart the hidden rules of daily life the way we map cities—pinpointing where tensions rise, where power shifts, and where cooperation wins? A…
-
AI in Health Care: Expert Insights on the Future of AI Practices, Policies, and Patient Safety
If you’ve felt like AI in health care went from buzzword to bedside overnight, you’re not imagining it. At a recent American Hospital Association panel, some of…
-
How AI Mapped 20,000 Everyday Interactions—and What It Reveals About Social Life
What if you could press pause on the chaos of everyday conversation—the banter with a friend, the tense chat with your boss, the quick apology to a…
-
Why “It’s Not Just X — It’s Y” Became the Dead Giveaway of AI Writing (and What to Do About It)
If you’ve been reading a lot of press releases, LinkedIn posts, or blog articles lately and keep stumbling on the phrase “It’s not just X — it’s…
-
How China Is Catching Up to the U.S. in AI: Chips, Talent, LLMs, and the Next Tech Superpower Race
What happens when the world’s manufacturing engine decides it also wants to lead the next big wave of intelligence? The global AI race isn’t just about who…
-
SpaceX Eyes a $60B Option to Acquire Cursor: The High-Stakes AI Partnership That Could Redefine Engineering
If you thought the AI race was heating up, SpaceX just poured rocket fuel on it. The company has formed a high-stakes partnership with Cursor—the fast-rising AI…
-
CBIZ Expands Microsoft AI Partnership: Foundry, Microsoft 365 Copilot, and Copilot Studio to Supercharge Productivity, Client Insights, and Talent
What happens when a national professional services powerhouse goes all-in on enterprise AI—with Microsoft as its copilot? You get a blueprint for the modern firm: agent-native operations,…
-
NeoCognition Raises $40M Seed to Build Human-Like, Self‑Learning AI Agents
What if the next AI you hire doesn’t come preprogrammed for a single task—but learns on the job like a new teammate? That’s the bet behind NeoCognition,…
-
Are AI‑Native Services the New Software? Inside Sequoia’s Bet, GV’s Big Round, and the Rise of Recursive Superintelligence
What if the next trillion-dollar category isn’t another SaaS app—but a service that feels like a teammate? That’s the provocative idea Sequoia Capital partner Julien Bek is…
-
AI Daily Brief – April 21, 2026: DeepMind’s Aggressive Push, Claude’s Lead, and the Cloud Infrastructure Stocks Powering the AI Boom
If you thought the AI race was cooling off, think again. Today’s biggest signal isn’t a new model release—it’s a strategic pivot. Reports indicate Sergey Brin is…
-
Anthropic’s Mythos Breach: Report Claims State-Sponsored Group Exploited Supply-Chain Zero‑Day
When a security tool built for elite defenders becomes the target, the stakes—and ironies—are impossible to ignore. That’s exactly what unfolded with Anthropic’s newly launched cybersecurity platform,…
-
Amazon’s $100B Anthropic Bet, OpenAI’s GPT-5.4-Cyber, and Google’s Agentic AI Pivot: The Week AI Grew Up
If you felt like the AI world shifted under your feet this week, you’re not alone. In a single news cycle, Amazon committed a jaw-dropping $100 billion…
-
OpenAI’s Existential Crossroads: Clean Energy and Ethical AI Drive 2026 Acquisitions
What if GPUs aren’t OpenAI’s biggest bottleneck? What if the limiting factors for frontier AI are, instead, two very human-made constraints: clean power and credible ethics? That’s…
-
AI Tool Predicts How New Drug Molecules Move—Before Expensive Lab Testing Even Begins
What if you could watch a brand-new drug molecule “swim” through a cell environment, bump into proteins, and either stick or slip away—without ever mixing a single…
-
Meta to Record Employees’ Keystrokes to Train AI: Privacy, Power, and the New Data Gold Rush
If you work in tech, your keyboard might soon be part of a training dataset. According to a report highlighted by TechCrunch and first surfaced by Reuters,…
-
The Most Interesting Startups at Google Cloud Next 2026: Why Inference Is the New AI Battleground
If you wanted a snapshot of where AI infrastructure is heading, Google Cloud Next 2026 in Las Vegas was the place to be. The message was loud…
-
Google Makes AI Agents the Core of Its Enterprise Strategy at Cloud Next — And Why It Matters for Every CIO
What if your spreadsheet could brief your sales team, resolve a customer ticket, draft a contract update, and book a follow-up—all before you sip your morning coffee?…
-
Google Cloud Next 2026 Ushers in the Agentic AI Era: Ironwood TPUs, A2A Protocol, and Workspace Studio Take Center Stage
What happens when AI agents stop being demos and start becoming the infrastructure of work? At Google Cloud Next 2026 in Las Vegas, that question wasn’t hypothetical…
-
Google Takes Aim at Nvidia: New Inference-Optimized AI Chips to Turbocharge AI at Scale
If you’ve felt like AI keeps getting smarter while your cloud bill keeps getting larger, you’re not alone. The explosion of AI apps has shifted the cost…
-
AI Daily Recap – April 22, 2026: Hype vs. Reality from Courtrooms to Orbit and MIT’s Roadmap for What’s Next
Ever feel like AI news oscillates between “robots will run the world next week” and “AI just tripped over its own shoelaces”? April 22, 2026, was one…
-
AI News Daily — April 22, 2026: OpenAI’s ChatGPT Images 2.0, SpaceX–Cursor Megadeal, and Meta’s Data Gambit Signal AI’s Push to Production
What do a faster, sharper image model, a potential $60B coding-assistant acquisition, and employee activity logs have in common? Together, they tell a story about AI’s new…
-
Google Cloud’s multi‑billion‑dollar bet on Mira Murati’s Thinking Machines Lab puts Nvidia’s GB300 front and center
What happens when a frontier AI startup obsessed with reinforcement learning gets priority access to some of the world’s most advanced AI chips—at cloud scale? According to…
-
Why Delta’s Ed Bastian Says Calling It “Artificial Intelligence” Is a Mistake—and What That Means for Aviation
If you wanted to make people nervous about new technology, what would you call it? According to Delta Air Lines CEO Ed Bastian, the very phrase “artificial…
-
It’s Time to Hit the Brakes on Runaway AI: A Pioneer’s UN Warning and What Comes Next
What happens when a technology advances faster than our ability to steer it? At the UN’s AI For Social Development Conference on April 22, 2026, a pioneering…
-
Do AI Language Models Understand the Real World? Brown University’s New Study Points to a Surprising “Yes” (At a Basic Level)
If you tell a chatbot, “A man is taller than the Eiffel Tower,” will it treat that as unlikely or flat-out impossible? And what if you say,…
-
Microsoft’s A$25 Billion AI Play in Australia: What It Means for Infrastructure, Security, and Skills
If you’re wondering how fast AI will reshape Australia’s economy, Microsoft just answered: very fast, and at very large scale. With a landmark A$25 billion (USD 18…
-
Why Nvidia Just Dumped $40B in OpenAI and Anthropic (2026): What’s Really Going On
If you blinked, you might have missed one of the most pivotal moves in the AI economy this decade. Nvidia—the chip titan powering today’s AI boom—just pulled…
-
UConn Health Minute: How AI Is Transforming Orthodontics for Faster, Smarter Smiles
What if your orthodontic treatment could be planned with near-surgical precision, monitored from your couch, and finished with fewer office visits—without compromising results? That’s not science fiction….
-
Americans Want AI on Campus—but Don’t Trust Colleges to Get It Right
Can two things be true at once? According to a new national survey, most Americans say colleges should teach artificial intelligence—and at the same time, most don’t…
-
Google Rebrands Vertex AI to Gemini Enterprise Agent Platform: A Full‑Stack Bet from TPU Chips to Your Inbox
What if your company could stand up AI agents that are faster, cheaper, and safer—without stitching together a dozen vendors or juggling brittle integrations? That’s the promise…
-
Don’t Rush AI into Elementary Classrooms: Why Indonesia’s Cautious Stance Could Future‑Proof Education
What if slowing down today is the smartest way to speed up tomorrow? While much of the world is racing to plug artificial intelligence into every corner…
-
New AI Tool ‘Mythos’ Is Rewriting Cybersecurity: Zero‑Day Discovery at Machine Speed and the Unraveling of Deterrence
What if a single AI could find more software vulnerabilities in a weekend than the world’s best red teams could uncover in a year? According to new…
-
Brain-like Hafnium Oxide Memristor Chip Could Cut AI Energy Use by 70%—A Neuromorphic Leap from Cambridge
What if the fastest way to make AI smarter wasn’t to build bigger data centers—but to build chips that think more like our brains? That’s the tantalizing…
-
AI Servers Are Draining the Power Chip Supply: PMIC and BMC Shortages Now Threaten “Regular” Servers
If you thought GPUs were the only hot commodity in AI, think again. The quiet heroes that feed and control those accelerators—power management integrated circuits (PMICs) and…
-
AI at the Precipice of an Aviation Revolution: How Boeing’s Next Airplane Could Be Built Smarter, Faster, and Safer
What if the next great leap in aircraft design doesn’t arrive on the factory floor—but in the data? That’s the premise transforming aerospace right now. According to…
-
Google DeepMind’s “Dynamic Reflections”: Real-Time Neural Rendering Meets Ray Tracing
If you’ve ever watched a shiny car glide past neon-lit windows at night or admired a glassy ocean reflecting a shifting sky, you’ve seen how mesmerizing dynamic…
-
Public Sector Accelerates AI in Cybersecurity: Balancing Privacy, Compliance, and Ethical Guardrails
What happens when the very institutions tasked with safeguarding citizens’ data turn to artificial intelligence to defend their own networks? In government and the wider public sector,…
-
Pennsylvania Treasurer’s DeepSeek AI Ban: What It Reveals About Government-Grade Cybersecurity, Vendor Risk, and the Future of Enterprise AI
What does it say about the state of AI security when a treasurer—someone tasked with safeguarding taxpayer dollars—steps in to ban a fast-rising AI platform across government…
-
OpenAI Disrupts Malicious AI Uses: Inside the February 2025 Threat Intelligence Report
What happens when the world’s most capable AI tools become a target—and a tool—for cybercriminals, influence operators, and surveillance teams? OpenAI’s February 2025 Threat Intelligence Report offers…
-
HaystackID Acquires eDiscovery AI: Supercharging GenAI for eDiscovery, Compliance, and Cyber Incident Response
What happens when a leading eDiscovery and investigations firm joins forces with a generative AI specialist purpose-built for legal and cyber workflows? If you’re in legal operations,…
-
Fortanix’s 2025 GenAI Data Security Report: Breach Risks Are Spiking—Here’s How to Build AI You Can Trust
If nearly every enterprise is racing to deploy GenAI, why are so many still getting breached? Fortanix’s 2025 GenAI Data Security Report, covered by Solutions Review, lands…
-
DeepSeek’s Open-Source LLM Surge Is Supercharging Cybersecurity Budgets: What CISOs Need to Do Now
What if the AI model that finally makes generative AI affordable is the same thing that blows up your security budget? That’s the paradox unfolding right now….
-
CISA Issues Urgent Warning: Actively Exploited iOS Zero‑Day CVE‑2025‑24200 Bypasses USB Restricted Mode
What if a locked iPhone or iPad wasn’t as locked down as you thought—just because someone could briefly plug in a cable? That’s the unsettling reality behind…
-
Carnegie Mellon and Anthropic Show AI Can Autonomously Launch Cyberattacks — What Security Leaders Must Do Now
What happens when AI stops being a co‑pilot and starts being the attacker? That’s not sci‑fi anymore. In a controlled research setting highlighted by the 2025 Cybersecurity…
-
$1.5B Bybit Crypto Heist Tied to North Korea’s Lazarus Group: What Happened, How It Happened, and What Comes Next
Imagine waking up to find that more than $1.5 billion in ETH and stETH vanished from one of the world’s most active crypto exchanges—pulled off in a…
-
OpenAI Bans ChatGPT Accounts Linked to Malicious Social Media Surveillance: What It Means for AI Security, Privacy, and Policy
What happens when cutting-edge AI meant to help people becomes the backbone of covert surveillance? That’s not a hypothetical anymore. According to a recent report from The…
-
Weekly Cybersecurity Highlights – February 22, 2025: Deepfakes, Weaponized LLMs, and the New Identity War
What if the next “breach” at your company doesn’t touch a single server—but still empties your accounts, reroutes your payroll, and shatters customer trust? That’s the unsettling…
-
Disrupting Malicious Use of AI Models: Inside OpenAI’s February 2025 Threat Report
What happens when bad actors treat AI like a Swiss Army knife—spinning up scams, mass-producing influence content, and debugging code all at once? OpenAI’s February 2025 threat…
-
AI and Cybersecurity in 2025: The New Frontier of Digital Defense (Phishing, Deepfakes, Zero Trust, and Autonomous SOCs)
If an AI can write code, hold conversations, and even mimic your voice, what’s stopping it from stealing your money—or saving your business? Welcome to the new…
-
Claude Code Vulnerabilities: How RCE and API Key Theft Can Trigger Just by Opening Untrusted Repositories
What if simply opening a project folder could hand over your API keys—or even your laptop—to an attacker? That’s the unsettling reality security researchers just spotlighted in…